mirror of
https://github.com/amidaware/tacticalrmm.git
synced 2026-04-26 06:55:52 +03:00
[GH-ISSUE #726] Information exposed through the Script Variables substitution #2404
Labels
No labels
In Process
bug
bug
dev-triage
documentation
duplicate
enhancement
fixed
good first issue
help wanted
integration
invalid
pull-request
question
requires agent update
security
ui tweak
wontfix
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference
starred/tacticalrmm#2404
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @NiceGuyIT on GitHub (Sep 21, 2021).
Original GitHub issue: https://github.com/amidaware/tacticalrmm/issues/726
Server Info (please complete the following information):
Installation Method:
Agent Info (please complete the following information):
Describe the bug
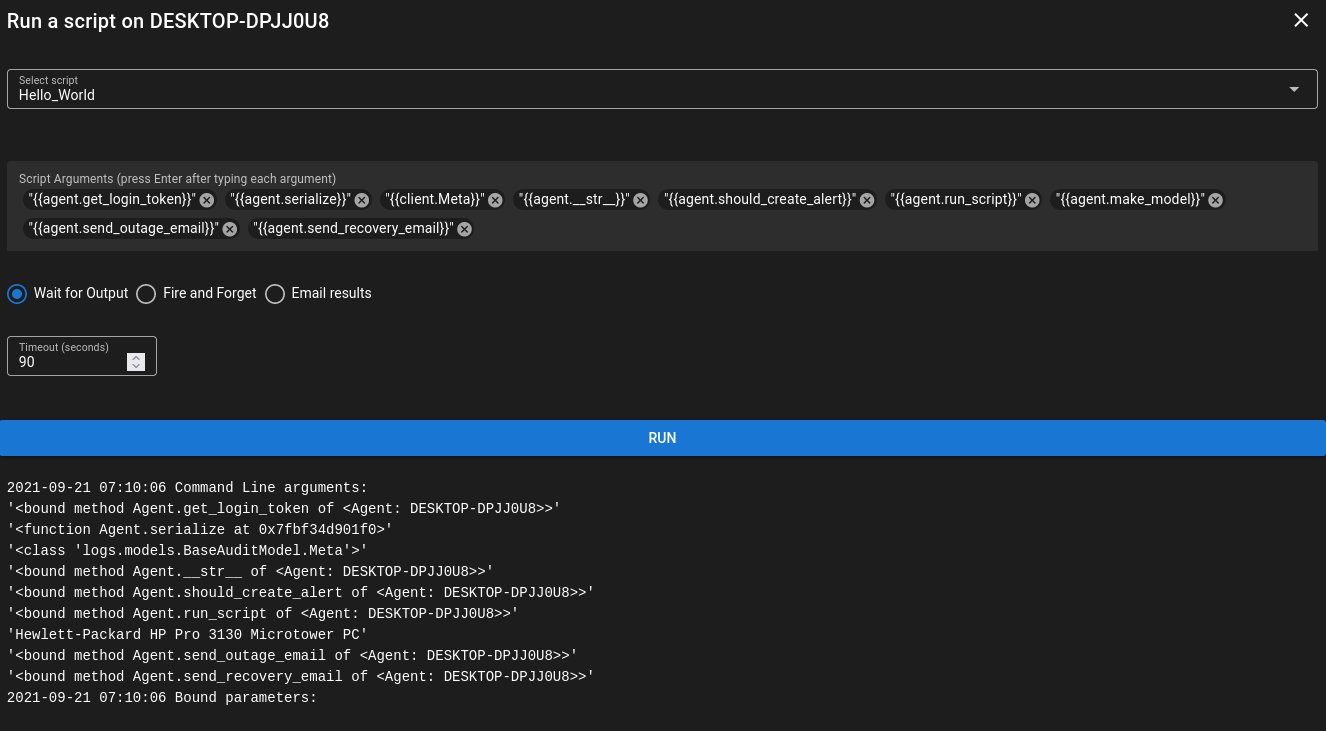
The script variables functionality exposes information that might not need to be exposed.
To Reproduce
Steps to reproduce the behavior:
Get-Timestampis a custom function to log the time, not a built-in cmdlet.Expected behavior
Methods and class names should not be exposed when running a script.
Screenshots
Additional context
While this isn't a true security issue since Tactical doesn't have user permissions, this has the possibility of becoming something bad in the future.
{{client.Meta}}exposes class names.{{agent.make_model}}returns the agent's make and model and is implemented as a method with@property, not an actual property. The other functions I checked returnbound method. Some of these functions are return useful information. My concern is two fold:agent.get_login_token.savemethod.Most of this is mitigated by Tactical returning the object representation as a string instead of executing the method and returning the results as a string. It would be nice if Tactical checked if the class property (script argument from the user) is an actual property or approved method and return nothing (or an error) if it's a class method not decorated as a
@propertyor another class name.@sadnub commented on GitHub (Sep 21, 2021):
That sounds like a feature to me! I don't think class names or other specifics in regards to the code is a concern because it is open source.
But like you said could lead to revealing sensitive information if a user of trmm wasn't supposed to view that. I think I am just using hasattr(obj, "prop_name") and getattr(obj, "prop_name"), so I can maybe do a check to see if the returned value is a function and not include that. I do want to keep the @property items exposed, because those could be useful