mirror of
https://github.com/NginxProxyManager/nginx-proxy-manager.git
synced 2026-04-26 01:45:54 +03:00
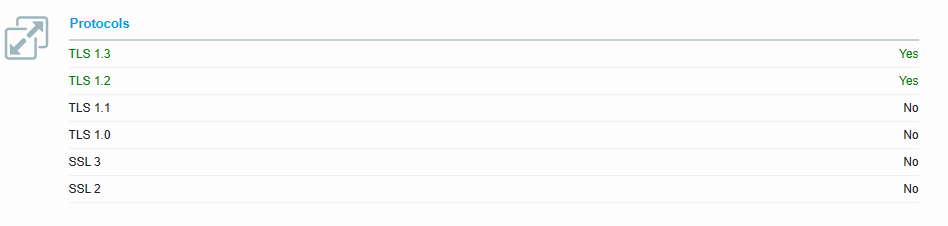
[GH-ISSUE #2823] TLS bug (TLS 1.0 & 1.1 offered - TLS 1.3 not offered) NMAP #1936
Labels
No labels
awaiting feedback
bug
cannot reproduce
dns provider request
duplicate
enhancement
enhancement
enhancement
good first issue
help wanted
invalid
need more info
no certbot plugin available
product-support
pull-request
question
stale
troll
upstream issue
v2
v2
v2
v3
wontfix
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference
starred/nginx-proxy-manager-NginxProxyManager#1936
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @the-hotmann on GitHub (Apr 13, 2023).
Original GitHub issue: https://github.com/NginxProxyManager/nginx-proxy-manager/issues/2823
This relates to:
Running onn latest 2.10.2
When I run:
nmap --script ssl-enum-ciphers -p 443 example.domain.tldI get this as response:
Problems:
TLS 1.0&TLS 1.1are both getting offered, even though they should be disabled. (#125)I have seen and checked the config
/etcnginx/conf.d/include/ssl-ciphers.confbut could not find the bug.Wanted:
nmapshould not report that the server is capable ofTLS 1.0&TLS 1.1at allnmapshould report that the server is capable ofTLS 1.3Thanks in advance! :)
P.S.: I am open for a discussion
@jebabin commented on GitHub (Apr 14, 2023):
As a workaround, try to add
ssl_protocols TLSv1.2 TLSv1.3;in /data/nginx/custom/http.conf it should at least fix the non working TLS 1.3 part@the-hotmann commented on GitHub (Apr 22, 2023):
Thanks! I will report back, once I implemented it.
However, that is actually the less important of the two issues.
It is more important not to offer
TLSv1.0andTLSv1.1, as these versions are insecure and pose a security risk.@wokkeltje13 commented on GitHub (Apr 22, 2023):
I have no /data/nginx/custom/http.conf file
@kingfisher77 commented on GitHub (Apr 25, 2023):
Have a look here.
nginx-proxy-manager is really a "Diva". Each update is a real risk...
@wokkeltje13 commented on GitHub (Apr 25, 2023):
tnx, got the diva providing TLS 1.3
@wokkeltje13 commented on GitHub (Apr 25, 2023):
For me there is no old TLS active, only 1.2 and 1.3
@kingfisher77 commented on GitHub (Apr 25, 2023):
I had to add
ssl_protocols TLSv1.2 TLSv1.3;/data/nginx/custom/http.conf@wokkeltje13 commented on GitHub (Apr 25, 2023):
This is what I did, but before only 1.2 was available, no 1.0 and 1.1
@nietzscheanic commented on GitHub (May 19, 2023):
pull request https://github.com/NginxProxyManager/nginx-proxy-manager/pull/2932
@stanthewizzard commented on GitHub (May 31, 2023):
Hello
I'm using http.conf
What would be the best cypher ?
Thanks
@dobbleg1000 commented on GitHub (Jun 3, 2023):
@stanthewizzard I would start a new issue for this question also dont include ssl_prefer_server_ciphers
as that is set elsewhere and will cause it to fail to start.
@github-actions[bot] commented on GitHub (Jan 22, 2024):
Issue is now considered stale. If you want to keep it open, please comment 👍
@Goldmaster commented on GitHub (Jul 28, 2024):
I have noticed that I get This server supports TLS 1.0 and TLS 1.1. Grade capped to B on ssl labs. Wonder if a pull request is needed to fix the issue?
@TimeJunkie01 commented on GitHub (Aug 13, 2024):
Turning off TLSv1 and TLSv1.1 is still an open issue. I am using v2.11.3.
@the-hotmann commented on GitHub (Sep 20, 2024):
@Goldmaster @TimeJunkie01
I had to adjust the config manually to fix the problem.
But this was not good enough for me in the long run, so I decided that I dont care and will just use a plain
nginx:1-alpine-slimdocker image and configure stuff myself.Can recommend this to everyone, as it make you understand the whole thing better and not rely on stuff, that you cant controll/manage.
For me this was a big problem due to security scans and alerts.
There are also other solutions out there, that do offer the same functionality (reverse proxying) with way more features, up-to-date config, secure defaults and additionally more dev-support. Just do some research, I dont want to talk this app down in its own issue-section.
@WarmWelcome commented on GitHub (Jan 27, 2025):
Are there any updates on this to disable 1.0-1.1 and only allow 1.2-1.3?