mirror of
https://github.com/lldap/lldap.git
synced 2026-04-25 16:25:55 +03:00
[GH-ISSUE #432] Getting it to work with Rancher on Kubernetes #164
Labels
No labels
backend
blocked
bug
cleanup
dependencies
docker
documentation
duplicate
enhancement
enhancement
frontend
github_actions
good first issue
help wanted
help wanted
integration
invalid
ldap
pull-request
question
rust
rust
tests
wontfix
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference
starred/lldap-lldap#164
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @Evantage-WS on GitHub (Feb 3, 2023).
Original GitHub issue: https://github.com/lldap/lldap/issues/432
Hi,
I have created a deployment on Kubernetes with your container and I am able to get it configured in Rancher and on a user level, it is working.
I am not an LDAP expert, so I am lost in what I should enter at a group level, are you able to help me?
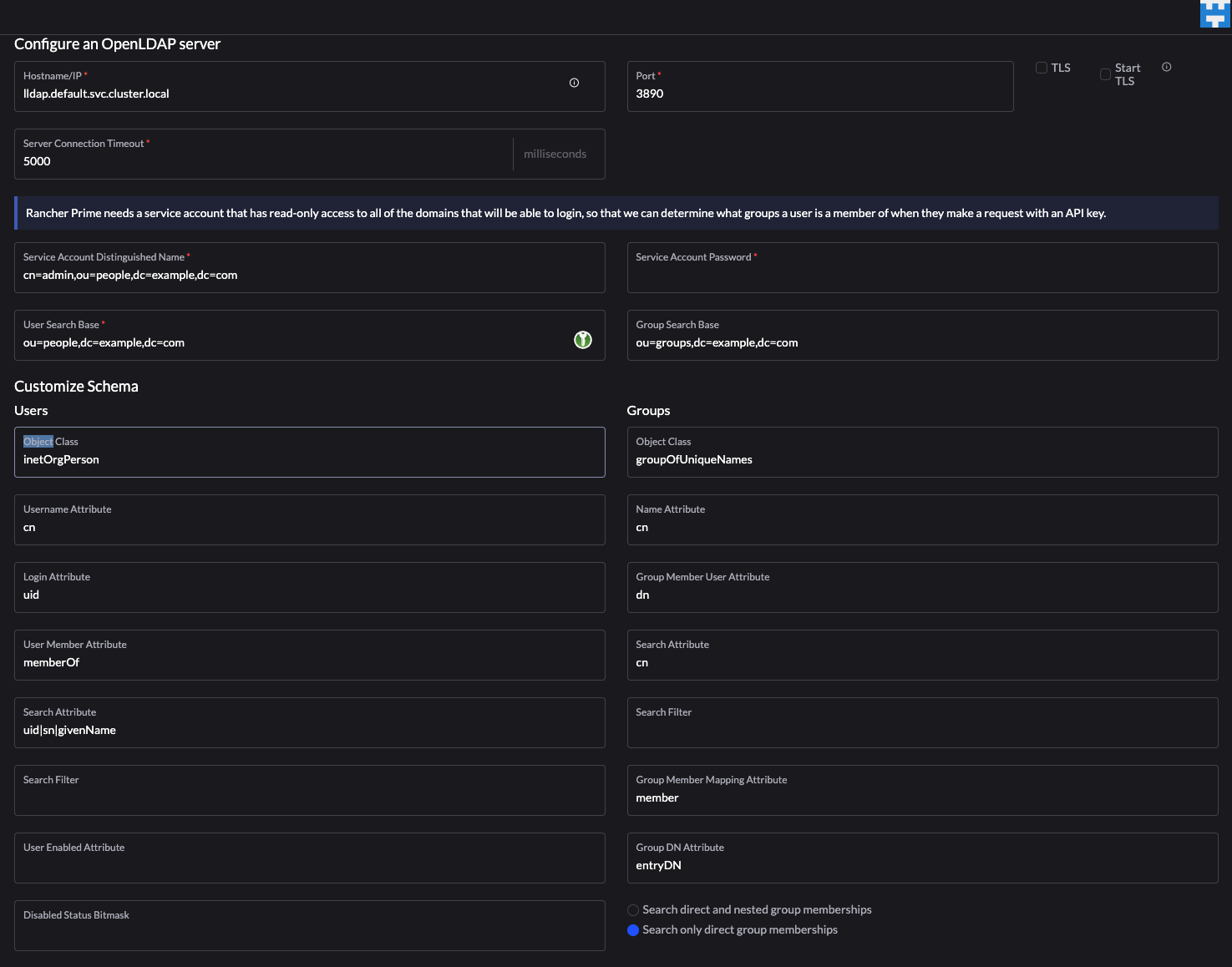
This is the config for LDAP in Rancher:

This config works, as long as i do not fill in the group details. when I do fill in ou=people,dc=example,dc=com at the Group Search Base, I do get an:
This is the log:
Could you be of assistance? Thanks!
@nitnelave commented on GitHub (Feb 6, 2023):
Hmm, it seems we don't support quite well
entryDNfor groups.I'll have a look, it should be fairly easy to add.
@Evantage-WS commented on GitHub (Feb 6, 2023):
@nitnelave,
Thanks, that would be great.
It is not clear if it is a problem in the code of just a naming thing, this because I can change the values in the LDAP/Group entries in Rancher to something your app supports and can get groups to work?
@nitnelave commented on GitHub (Feb 6, 2023):
Yeah, actually, can you try with just
dninstead ofentryDN?A small note: object class should be
groupOfUniqueNames(a bit pedantic maybe but more future-proof)@Evantage-WS commented on GitHub (Feb 6, 2023):
Hi @nitnelave, done, it is accepting the config and but still errors in the log, also with groupOfUniqueNames, it is complaining about it and no group info in Rancher. Could you please look at this?
Current config:
@nitnelave commented on GitHub (Feb 6, 2023):
The
groupDNAttributeat the bottom should also bedn@Evantage-WS commented on GitHub (Feb 6, 2023):
Done, but no luck.
The lldap log:
@nitnelave commented on GitHub (Feb 6, 2023):
Hmm, that's the log from the login, not the group search
@Evantage-WS commented on GitHub (Feb 9, 2023):
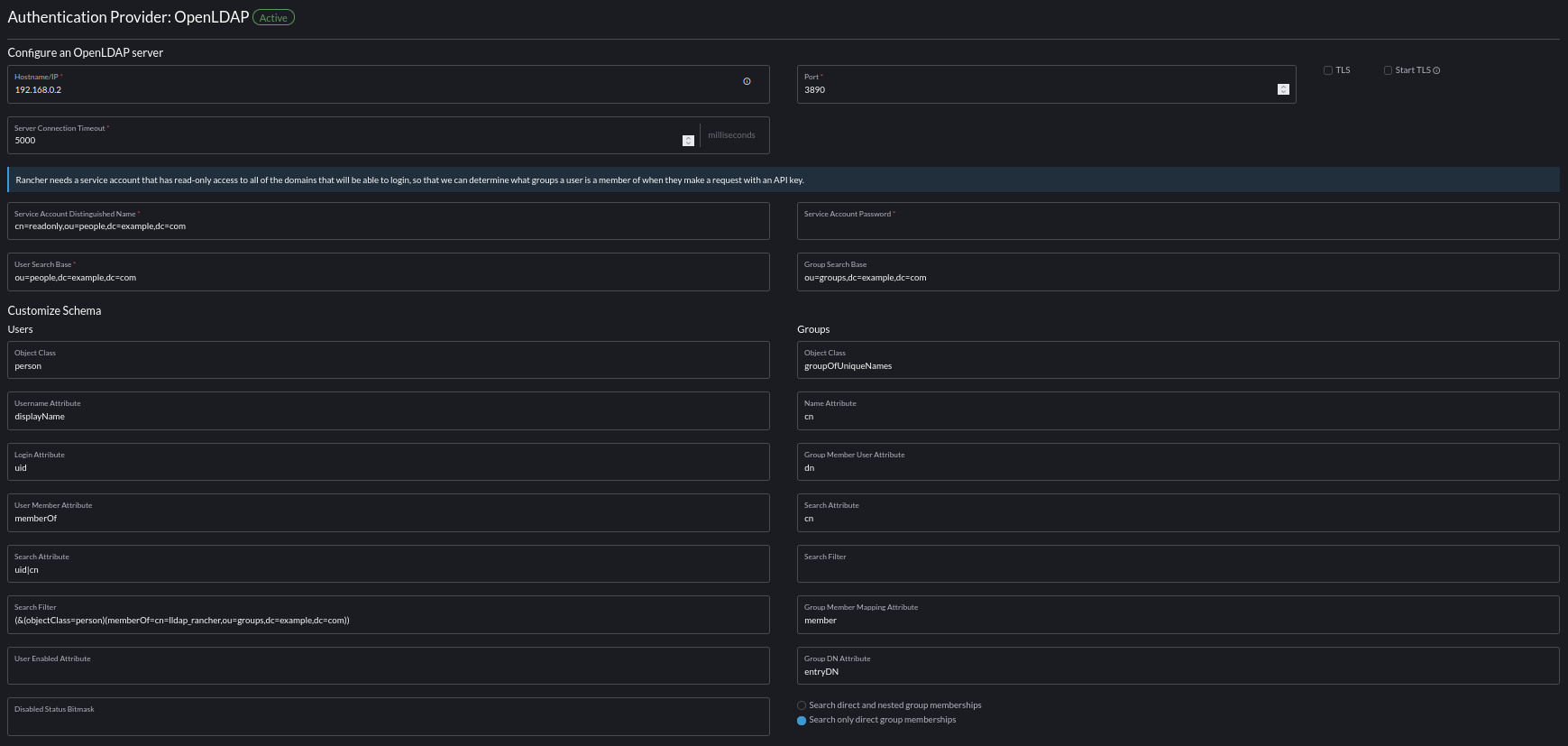
Hi @nitnelave, I did a reinstall of the Kubernetes cluster and installed lldap again. The weird thing is that the user lookup is also failing now with this config:
@nitnelave commented on GitHub (Feb 9, 2023):
That's weird, now it's using
SubStringto search for users instead of exact matches. Did you change anything else related to that?Otherwise, you can try to remove the Search Attribute and add a Search Filter instead:
(|(uid=%s)(sn=%s)(givenName=%s))or whatever placeholder they use instead of%s.@Evantage-WS commented on GitHub (Feb 9, 2023):
No, did not change anything. All is the same version and entered exactly as in the screenprint. Unfortunally, when I empty the Search Attribute field, it will come back with "uid|sn|givenName" value. I did add "(|(uid=%s)(sn=%s)(givenName=%s))", but still the same error.
I am unable to find out about the placeholder and the Rancher server is logging nothing when contacting the LLDAP server.
I got it all working with OpenLDAP, users and groups, I really would like to get this working with LLDAP, because OpenLDAP is huge and I just need a simple, fast working LDAP server.
@nitnelave commented on GitHub (Feb 9, 2023):
I had a look at their docs (and the code), and it seems that we can't get around the
SubStringfilter. However, it's just when adding users/groups, not when logging in. Logging in should still work, normally. Can you post a full clean LLDAP log with a single login attempt?In the meantime, you can open an issue to add support for
SubString.@Evantage-WS commented on GitHub (Feb 9, 2023):
Hi @nitnelave, I can configure it with the admin user and that connection is working. This is the log from the succesful login into Rancher with the admin user from lldap.
I created a second user, called testuser and In Rancher I did a search for it, which fails. This is the log:
The entry field in Rancher does search for users and groups, I do not get either.
I do not use Rancher to create users in LLDAP, only searching in LLDAP. I will raise an issue for support for SubString. Can you tell me an estimate? I do have a demo in about a week. If that is not possible I have to go with OpenLDAP :-(
Thanks sofar, I hope the logs will help to solve this.
BTW, you can run Rancher in Docker, maybe this helps you to get this working? See https://ranchermanager.docs.rancher.com/reference-guides/single-node-rancher-in-docker/http-proxy-configuration
Thanks!
@nitnelave commented on GitHub (Feb 9, 2023):
Yeah, searching for users will not work without substring.
I can't really give you an estimate of when I'll implement it, because I don't know in general how much time I'll spend on this free, open source project :)
And this issue is not my top priority either. If you want to help by adding support for it yourself, I'd help by reviewing the PR! In that case things can go pretty fast.
Otherwise, a week is not realistic.
If you want another simple LDAP server, you can try kanidm as well.
@Evantage-WS commented on GitHub (Feb 9, 2023):
I completely understand, appreciate all your work and support. I will wait for your fix, no rush.
I will take a look at kanidm as well, thanks!
@martadinata666 commented on GitHub (Feb 9, 2023):
Pretty curious about this so im trying, and it working?
not really sure, instead openldap, this is freeipa. Should be pretty much alike? not realy sure about the differences.search filteror i getfound '=', expected: !, identifier, or 'end of string'Username Attributesfrom the docs it about display name.Rancher OpenLDAP docs
@nitnelave commented on GitHub (Feb 9, 2023):
What if you put
uid|cnin the search attributes? Does that break it?@martadinata666 commented on GitHub (Feb 9, 2023):
Also works. Im trying with openLDAP auth type, also works.
@nitnelave commented on GitHub (Feb 9, 2023):
And just checking, searching for users also works?
@martadinata666 commented on GitHub (Feb 9, 2023):
I don't know how to trigger it. , or I don't find it in rancher UI
literally just deploy a few hours out of curiosity🤔 But I can log in with a few different UID as long as it is in one group. Looking for OP to test it out, it seems OP is more proficient using rancher ☕@Evantage-WS commented on GitHub (Feb 10, 2023):
@martadinata666, thanks for adding this, but unfortunally, it has the same problem as I have, Searching does not work with this example. I tried it without the group as well in the searchfilter.
@martadinata666 commented on GitHub (Feb 10, 2023):
confused with this
searching, where do I trigger it? or what should I do? 🤔@Evantage-WS commented on GitHub (Feb 10, 2023):
In Rancher, at the OpenLDAP authentication provider, change the field on the left to the second choice and on the right, at Add member, you can do a search for an user or group. You only see this screen when the OpenLDAP has a succesful connection.
@nitnelave commented on GitHub (Feb 13, 2023):
@Evantage-WS Can you try again with the latest image? It has support for SubString.
@Evantage-WS commented on GitHub (Feb 14, 2023):
Hi @nitnelave, nice, it is working. I can search for users and groups. I can login as a member of a new created group. Thanks!
@nitnelave commented on GitHub (Feb 14, 2023):
Do you want to submit a PR sharing your config?
@Evantage-WS commented on GitHub (Feb 16, 2023):
Hi, I will certainly do that, present Corona hit me, so give me a few days.