mirror of
https://github.com/hoppscotch/hoppscotch.git
synced 2026-04-26 01:06:00 +03:00
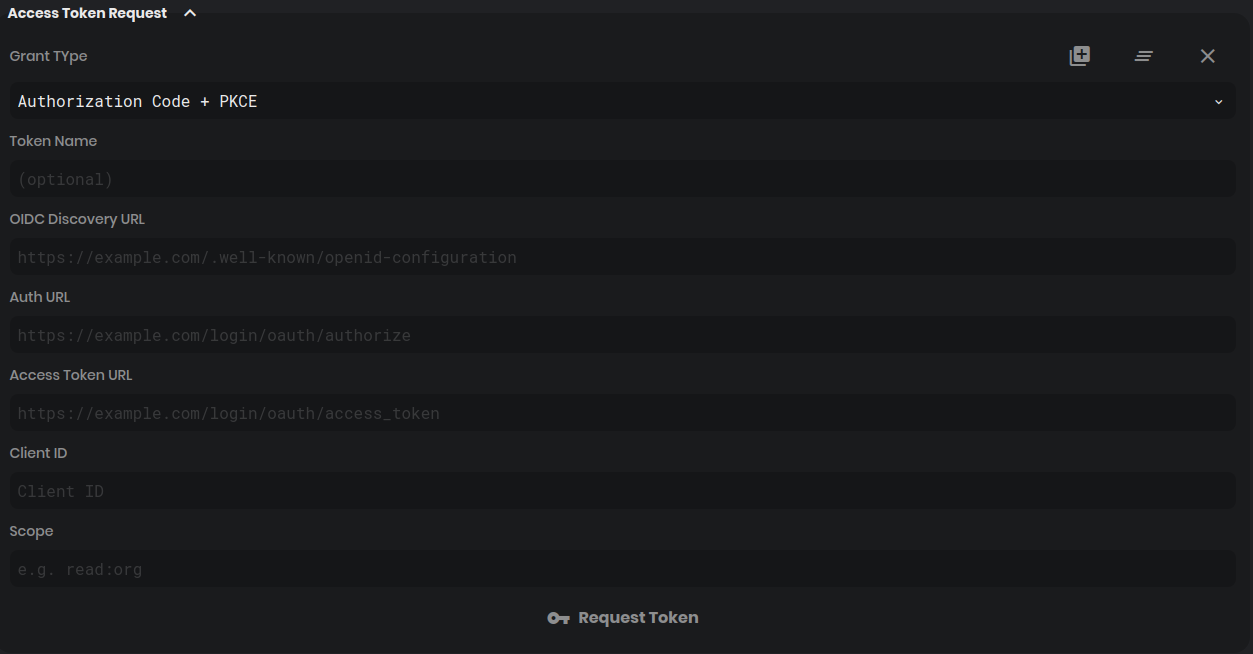
[GH-ISSUE #874] [feature] different OAuth-2 grant types #305
Labels
No labels
CodeDay
a11y
browser limited
bug
bug fix
cli
core
critical
design
desktop
discussion
docker
documentation
duplicate
enterprise
feature
feature
fosshack
future
good first issue
hacktoberfest
help wanted
i18n
invalid
major
minor
need information
need testing
not applicable to hoppscotch
not reproducible
pull-request
question
refactor
resolved
sandbox
self-host
spam
stale
testmu
wip
wont fix
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference
starred/hoppscotch#305
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @raha1923 on GitHub (May 14, 2020).
Original GitHub issue: https://github.com/hoppscotch/hoppscotch/issues/874
Is your feature request related to a problem? Please describe.
I'm trying to use postWoman in my private project as a standalone API console. The problem is that the APIs that I want to use are using different flows to get the access token, not just code-flow.
Describe the solution you'd like
PostWoman OAuth-2 getNewToken would be great if we just let the user choose what grant type wants to use and implement the other flows of getting access token.
I can help if you want to implement it asap. just please let me know if you do agree with the idea.
@liyasthomas commented on GitHub (May 14, 2020):
@raha1923 letting user to choose what grant type wants to use makes sense. We're open on making the OAuth workflow better. Let's implement this.
@raha1923 commented on GitHub (May 14, 2020):
@liyasthomas it's great.
I'm reading and exploring the project and trying to find out how things are working. I think it would be easy for me to develop its functionality, but I need help to make it's UI better and more user friendly.
@liyasthomas commented on GitHub (May 14, 2020):
Okay, sounds fine. Let me know when the basic mvp is ready. I'll do the UI.
@raha1923 commented on GitHub (May 14, 2020):
@liyasthomas could you please tell me why you have used PKCE?
@liyasthomas commented on GitHub (May 14, 2020):
OpenID and PKCE was one of the most requested feature regarding OAuth.
@raha1923 commented on GitHub (May 14, 2020):
Well, I'm going to develop the following flows (sorted by priority):
@raha1923 commented on GitHub (May 19, 2020):
hey @liyasthomas
There is an important thing about implementing other flows of oAuth and it's the security issues that may cause a sort of problem. I'm going to add fields like client-credential and client-secret and ask the user to fill them to make that flows works fine and right and let the user choose to accept the risks or not if they accept the feature would be accessible.
Is it ok???
@liyasthomas commented on GitHub (May 19, 2020):
@raha1923 it sounds fine to prompt users to enter
credentials.@liyasthomas commented on GitHub (May 29, 2020):
@raha1923 just thought I'd ping you to know the status of this issue. are you in need of any help from me?
@raha1923 commented on GitHub (May 31, 2020):
@liyasthomas thank you
well I'm trying to find the postwoman useful for our special use case, we are going to use postwoman in a private local network without internet access. so in that case we can't create collections and etc.
I've created a to connect to and send and receive data from. I'm storing data in Mongo with exact schemas. After that, I will start developing the other grant types.
@raha1923 commented on GitHub (Jun 12, 2020):
WIP
@RodolpheGohard commented on GitHub (Sep 14, 2020):
Hello @raha1923 , thanks for working on this issue, I would love to see client_credentials implemented. Is the work still ongoing on it ?
@raha1923 commented on GitHub (Sep 22, 2020):
Hi, I'm here and just looking for a proper time to clean the code and commit and push what I have implemented on the project to make it work with other grant types in oAuth 2. just need time to focus on the subject and clean, commit and push, please be patient. It worth it.
@2Dews commented on GitHub (Jan 26, 2021):
@raha1923 would love to have implicit grant type. Any chance you could push your work as a branch, even if its not finished?
@mdbetancourt commented on GitHub (Jan 12, 2022):
is this issue abandoned? would love to have client credentials
@mdbetancourt commented on GitHub (Mar 22, 2022):
since this issue isn't moving forward, I've implemented my own "client credential" grant type, tomorrow I'll do a pull request
@lordvlad commented on GitHub (Aug 3, 2023):
would be nice to have this 👍
@FerrarisIV commented on GitHub (Aug 20, 2023):
Have news about it? I am not be able to generate token for Keycloak. In Postman I can set Client Credentials as GrantType. Have someone a solution or workaround?
@lordvlad commented on GitHub (Aug 20, 2023):
I got a fork with working client credentials and also an option to send
client credentials in header (as opposed to body). I haven't published the
fork yet. Can do that in the week of Aug 28th, once back from vacation.
Don't have time for a "beautiful" ui or tests though.
On Sun, Aug 20, 2023, 10:42 Mauro @.***> wrote:
@FerrarisIV commented on GitHub (Aug 20, 2023):
Yes of course i will wait. Enjoy your holidays :)
@lordvlad commented on GitHub (Aug 28, 2023):
Got the draft here: https://github.com/hoppscotch/hoppscotch/pull/3298
Requires a review, updating the documentation and updating tests, for which I unfortunately have zero resources.
@mduboisachieve commented on GitHub (Oct 12, 2024):
I know this is an old issue but was @lordvlad 's proposal abandoned? according to the oauth 2 spec (https://datatracker.ietf.org/doc/html/rfc6749#section-2.3)
the current default behavior sends the credentials in the request body. It would be nice to at least have the option to use basic auth (though it should probably be the default)
@norcino commented on GitHub (Oct 30, 2024):
I am working on the design of an authorization service based on OAUTH2, this will be used by all APIs in my company and will support only client credentials flow but not using client authentication via username and password (basic).
This approach is not recommended, the flow will be more complicated and cumbersome but using a signed JWT token will be soon much more popular than might be right now.
https://www.ietf.org/archive/id/draft-ietf-oauth-v2-1-04.html#name-client-authentication
@alishah730 commented on GitHub (May 15, 2025):
authcode + PKCE still not working?
@jamesgeorge007 commented on GitHub (Nov 27, 2025):
Hi, Hoppscotch now supports all major
OAuth 2.0grant types as originally requested.Please see the authorization documentation for configuration details and usage instructions.
Note: OAuth 2.0 workflows are not fully supported in the Desktop application yet and remain a work in progress for that platform.
Closing this issue as the requested grant types are now available in the web platforms. If you're experiencing issues with a specific grant type or workflow, please open a new issue with detailed information about the problem
@jazuntee commented on GitHub (Dec 18, 2025):
@jamesgeorge007 is there another issue that is tracking the OAuth 2.0 support in the desktop application?