mirror of
https://github.com/hoppscotch/hoppscotch.git
synced 2026-04-26 01:06:00 +03:00
[PR #476] [MERGED] OAuth 2.0/OIDC Access Token Retrieval Support #2644
Labels
No labels
CodeDay
a11y
browser limited
bug
bug fix
cli
core
critical
design
desktop
discussion
docker
documentation
duplicate
enterprise
feature
feature
fosshack
future
good first issue
hacktoberfest
help wanted
i18n
invalid
major
minor
need information
need testing
not applicable to hoppscotch
not reproducible
pull-request
question
refactor
resolved
sandbox
self-host
spam
stale
testmu
wip
wont fix
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference
starred/hoppscotch#2644
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
📋 Pull Request Information
Original PR: https://github.com/hoppscotch/hoppscotch/pull/476
Author: @reefqi037
Created: 1/7/2020
Status: ✅ Merged
Merged: 1/7/2020
Merged by: @liyasthomas
Base:
master← Head:feature/oauth-support📝 Commits (10+)
d24b917added oauth token ui5377c69add oauth handlerb98d907fix token placement2e7e40cdisplay error & disable input based on user input83a20bdimplement oidc discovery2a818dccomment correctiondf48e85added token managementsf847cbeAdded token management161c0b7added token request management9d56af4Merge branch 'master' into feature/oauth-support📊 Changes
6 files changed (+764 additions, -8 deletions)
View changed files
➕
assets/js/oauth.js(+175 -0)📝
lang/en-US.js(+21 -1)📝
package-lock.json(+1 -1)📝
pages/index.vue(+531 -6)📝
store/mutations.js(+24 -0)📝
store/state.js(+12 -0)📄 Description
This PR adds OAuth2.0/OIDC Access Token retrieval function to Postwoman 🎉
Main Feature
With this feature, OAuth 2.0 access token can be retrieved directly from inside Postwoman.
Since Postwoman is a web-based SPA, it have no way to hide client secret used in the normal OAuth 2.0 flows. Therefore, only Authorization Code Flow + PKCE is implemented.
Additional Features
Screenshots
Main UI

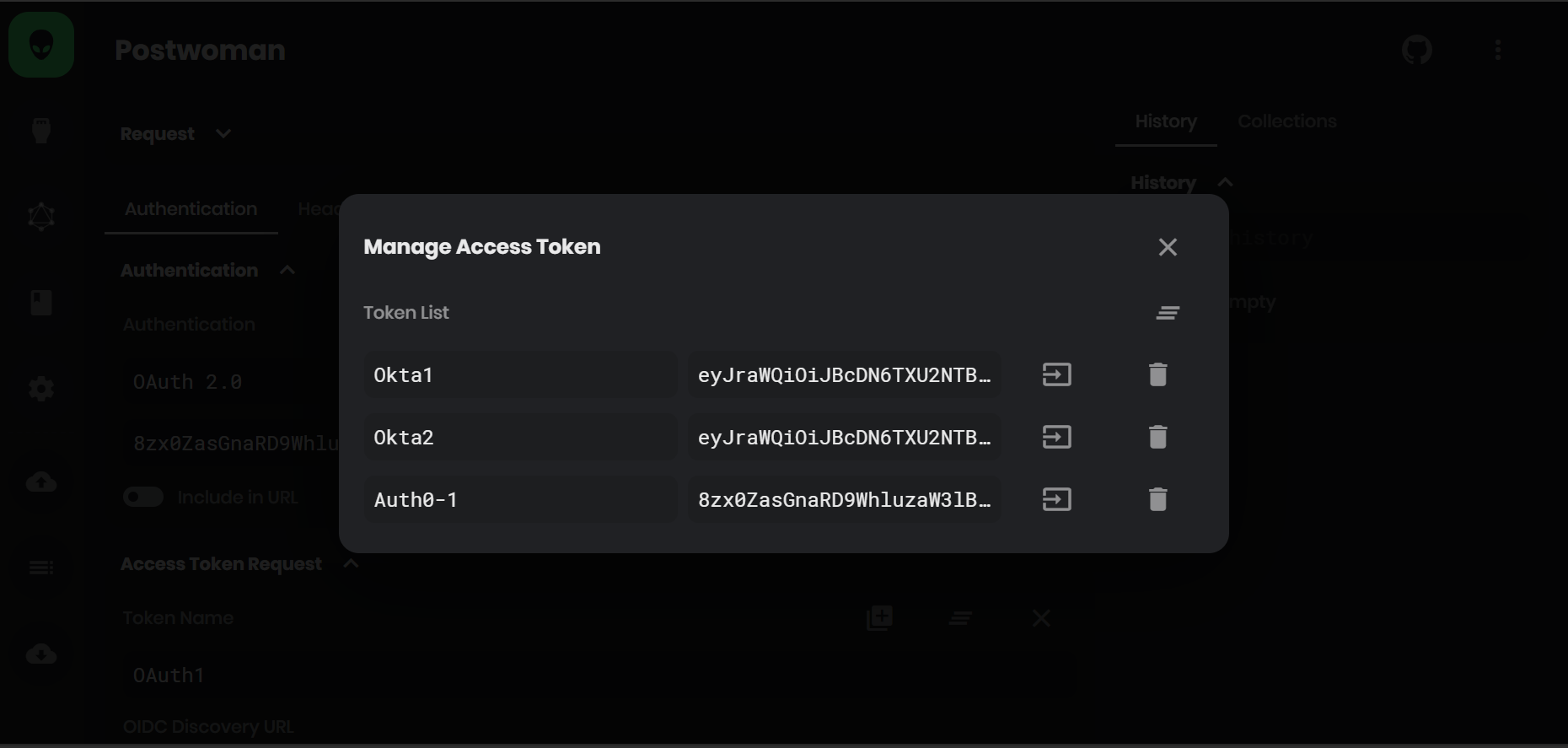
Access Token Management UI
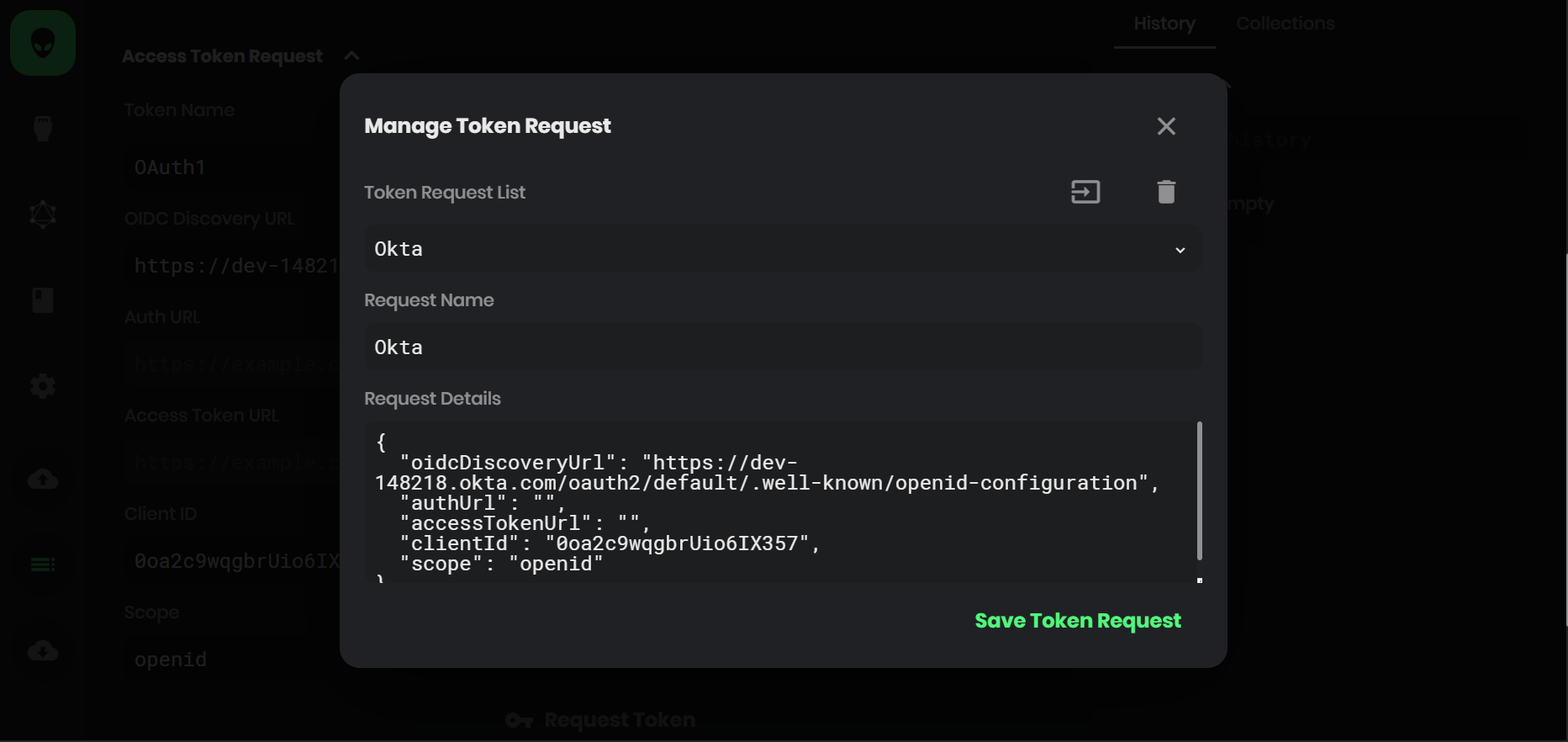
Token Request Management UI
Limitations
There should be room for improvements but for the time being, I think the core functions here should works ( tested with Okta and Auth0 as Service Providers ). Feel free to suggest and improve 👨💻 👩💻 🚀
fixes #337
🔄 This issue represents a GitHub Pull Request. It cannot be merged through Gitea due to API limitations.