mirror of
https://github.com/albertito/dnss.git
synced 2026-04-26 18:05:57 +03:00
[GH-ISSUE #11] Work with default(google) but not with others #11
Labels
No labels
enhancement
enhancement
pull-request
question
question
wontfix
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference
starred/dnss#11
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @sebaxakerhtc on GitHub (Jun 30, 2022).
Original GitHub issue: https://github.com/albertito/dnss/issues/11
Originally assigned to: @albertito on GitHub.
Hi there, nice project!
I found this today and i think is awesome project!
But, i try to use it and i can't get it working with custom DoH
This works fine:
sudo dnss -enable_dns_to_httpsThis works fine too (by IP, but that's wrong):
sudo dnss -enable_dns_to_https -https_upstream "https://1.1.1.1/dns-query"But this is not:
sudo dnss -enable_dns_to_https -https_upstream "https://cloudflare-dns.com/dns-query"And this is not work:
Of cource it doesn't work with Quad9 and my own DoH
Another good idea to add helpful info to readme:
To get it working you should disable and stop original resolver which use port 53
This happens if not
I hope you can help.
Cheers!
@albertito commented on GitHub (Jun 30, 2022):
Thanks for reporting this!
There are integration tests in
tests/external.shwhich validate that dnss works with some of the public providers, including all the ones you mentioned (cloudflare via ip, cloudflare via domain, quad9). They're run on each commit and weekly from gitlab-ci, and I just run them again from my workstation, and they are all passing.So I wonder what's causing the failures for you.
Can you run dnss with
-v=3, which enables debug logging, and paste the output here so we can debug this further?Thank you!
@sebaxakerhtc commented on GitHub (Jul 1, 2022):
-v (1,2,3) do not show additional info.
Command:
sudo dnss -enable_dns_to_https -https_upstream "https://cloudflare-dns.com/dns-query" -force_mode DoH -v 3Output when i try to open any website:
@sebaxakerhtc commented on GitHub (Jul 1, 2022):
It work with only one additional option
-fallback_domains stringMy mistake was on "dot" at the end of domain name
I should use
dns.quad9.net.instead ofdns.quad9.net@sebaxakerhtc commented on GitHub (Jul 1, 2022):
@albertito
can you explain how to use 2 ip addresses in
Can i use it like
? Will it work normally?
I'm a paranoic who want to use only my selfhosted DoT, DoH and DNS.
I don't want to use any default(google) requests. Even to request where is my DoH located.
Thank you!
@albertito commented on GitHub (Jul 2, 2022):
What version of dnss are you using?
-fallback_domainsis deprecated and hasn't been doing anything for a while. Maybe you're running an older version?As for your latter question: only one
-fallback_upstreamvalue is allowed. If more than one is present, the last one will be used.If you want to completely self-host, which is totally supported by dnss, you just need to set
-fallback_upstreamand-https_upstreamto the servers of your choosing. dnss shouldn't contact anything else.And you can also use dnss as the DoH server. You have to set
-enable_https_to_dnsand then the DNS server to use, and TLS certs (or-insecure_http_serverif you're running it behind your own proxy).I hope this helps! Thanks!
@sebaxakerhtc commented on GitHub (Jul 2, 2022):
From apt | Ubuntu 22.04
That's sad. Can you add support for second IP? For redundancy.
If one of servers is down - it still will work
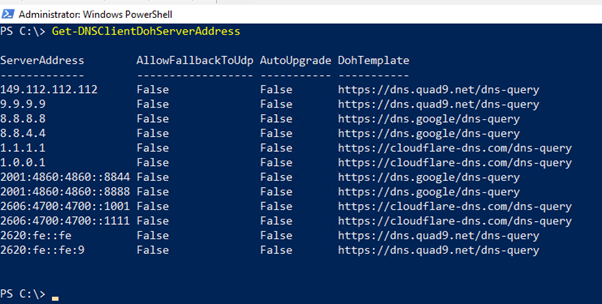
Even windows have this settings LoL
@albertito commented on GitHub (Jul 2, 2022):
Ah! That would explain the issue you're seeing. The problem was fixed in commit
5567591e91in 2021-03.I will work with Debian folks to get that package updated. I suggest you build a newer version built from the
masterbranch, then that option shouldn't be needed.And yeah, adding an option for multiple fallbacks sound reasonable, I will add it to the TODO list. Thanks!
@sebaxakerhtc commented on GitHub (Jul 2, 2022):
Builded successfully master with GO.
Now I see "deprecated"
It will be great!
Thank you so much!