mirror of
https://github.com/s3fs-fuse/s3fs-fuse.git
synced 2026-04-25 13:26:00 +03:00
[GH-ISSUE #241] IAM_Role Cross Account - full ARN syntax #129
Labels
No labels
bug
bug
dataloss
duplicate
enhancement
feature request
help wanted
invalid
need info
performance
pull-request
question
question
testing
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference
starred/s3fs-fuse#129
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @marcanthony on GitHub (Aug 17, 2015).
Original GitHub issue: https://github.com/s3fs-fuse/s3fs-fuse/issues/241
S3FS cant seem to use the FULL ARN of an IAM ROLE
This is critical to use s3fs to assume a role in another account for correct object ownership (this critical for buckets with replication enabled)
$> s3fs -d -d bucket /mnt/s3fs/bucket/ -o rw,nosuid,nodev,allow_other,stat_cache_expire=1,iam_role=arn:aws:iam::XXXXXXXXX:role/myrole,d efault_acl=public-read
--error
max_readahead=0x00020000
s3fs: Failed to check IAM role name(arn:aws:iam::##########:role/my-role).
@ggtakec commented on GitHub (Oct 1, 2015):
@marcanthony
I think s3fs need only IAM role name, not need full ARN.
s3fs call following URL for getting AccessKeyId & SecretAccessKey & Token by IAM role.
This result is following(example):
we can call “http://169.254.169.254/latest/meta-data/iam/info/“ and get following result.
But we do not need to check InstanceProfileArn because “security-credentials” result is get at only security permit.
Then iam_role option requires only IAM role name.
Please tell me if my thinking or usage IAM role for s3fs is wrong.
Thanks in advance for your help.
@marcanthony commented on GitHub (Oct 2, 2015):
The full ARN would permit the IAM ROLE in another AWS Account and Permit
Cross Region Bucket replication Ownership to work.
@ggtakec commented on GitHub (Oct 3, 2015):
I think you are correct about using role, but...
I think that you have set an IAM role at launching your EC2 instance for controlling s3fs by IAM role.
s3fs gets the security information by the IAM role on your EC2 instance, it is specified at launching.
It means that s3fs gets the role information that is specified in the instance rather than the user.
It gets by accessing the following URL from within the instance.
In other words, the s3fs to check is the IAM roles assigned to EC2, not the role assigned to the user.
s3fs can not be another access control AWS user with IAM role.
So that, iam_role option requires only IAM role name.
Following document explains about this.
Regards,
@marcanthony commented on GitHub (Oct 4, 2015):
What I am saying is currently the s3fs codebase assumes the IAM Role is from the EC2 instance launched on.
What I am suggesting is permit the FULL ARN
Check for ARN syntax
https://github.com/s3fs-fuse/s3fs-fuse/search?utf8=✓&q=IAM_CRED_URL&type=Code
Set it (don't assume local IAM role only)
string S3fsCurl::SetIAMRole(const char* role)
{
string old = S3fsCurl::IAM_role;
S3fsCurl::IAM_role = role ? role : "";
return old;
}
http://docs.aws.amazon.com/IAM/latest/UserGuide/walkthru_cross-account-with-roles.html
Why is cross account useful?
We have servers in AWS Account A that have authority on Buckets in Account's B, C and D.
In Accounts B, C and D we have bucket replication and versioning enabled. So for example:
Account B, Bucket 1 (region us-west-2) and Bucket 1 replicated (region us-east-1).
From Account A we U/L to Bucket 1 in Account B and its replicated by the STS/S3 service for Replication to occur the Account B must be the owner or have rights to the objects in Bucket 1.
Hence if you can do the full ARN we can use delegated roles to another account and or region.
This permits many use case other then the example just given.
@ggtakec commented on GitHub (Oct 6, 2015):
I think that now s3fs could not support full ARN IAM role without big change codes.
Because s3fs uses static URL access for getting simple security data by only IAM role name.
If full ARN is supported, I think s3fs access to IAM role API and AWS user, etc.
Instead of that change, if you can, s3fs uses IAM role name only yet, and you can associate AWS users to that IAM role.
Regards,
@ggtakec commented on GitHub (Mar 30, 2019):
We kept this issue open for a long time.
I will close this, but if the problem persists, please reopen or post a new issue.
@gitcrunch commented on GitHub (Apr 21, 2019):
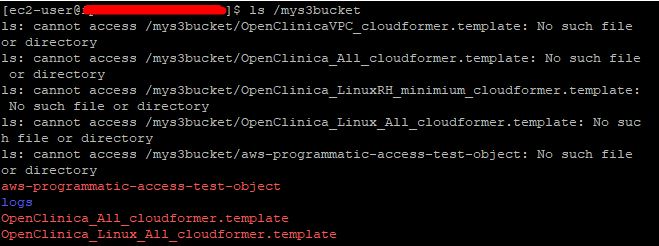
Although this discussion has been closed, I am trying my luck. I had the similar issue to access S3 in the other account B that is mounted on EC2 instance of account A. It seemed bucket was mounted. but get the error message "cannot access" even though the content of bucket was listed correctly. Then SFTP into the instance and able to see the mounted bucket folder and subfolder (of S3 in account B). But no files were displayed. Didn't quite understand the difference between full arn and role name only.
@ggtakec commented on GitHub (Apr 22, 2019):
@gitcrunch It seems to depend on the setting of IAM(access permission about HEAD/READ/POST/etc).
Another way, the latest master branch is compatible with AWS STS TOKEN, so it might help you.
@and3rson commented on GitHub (Aug 10, 2021):
Same issue here. I'm trying to assume role from a different account like this:
s3fsjust gets stuck on "IAM Access Token refreshing..."I've also tried to fetch the credentials manually (via
aws sts assume-role) before runnings3fs, but those includeSessionTokenwhichs3fsdoes not accept.EDIT: Just found the
use_session_tokenoption. Getting this in logs now:...which means credentials are getting picked up. However I'm still getting 403. Do I need to provide anything else beside
AWSACCESSKEYID,AWSSECRETACCESSKEYandAWS_SESSION_TOKEN?@srinisakh commented on GitHub (Dec 3, 2021):
iam_role option is used to retrieve credentials from instance metadata. AWS_SESSION_TOKEN need to be AWSSESSIONTOKEN without
_also I had to remove the path specification, just give bucket name. This is with s3fs v1.86
@rads18 commented on GitHub (Jul 11, 2022):
@srinisakh were you able to successfully mount bucket cross account?,
like bucketA in account A mount at EC2 in account B
i am not using IAM roles in the test phase but user account key/secret with no luck cross account. The AWS S3 cp/mv work fine cross account.