mirror of
https://github.com/ciur/papermerge.git
synced 2026-04-25 12:05:58 +03:00
[GH-ISSUE #271] Cross Site Scripting On Tags (https://demo.papermerge.com/admin/tags) #219
Labels
No labels
2.1
3.0
3.0.1
3.0.2
3.0.3
3.0.3
3.1
3.2
3.2
3.3
3.5
3.x
Fixed. Waiting for feedback.
Fixed. Waiting for feedback.
UX
Version 2.1 - alpha
XSS
announcement
beta
blocker
bug
cannot reproduce
confirmed
confirmed
critical
demo
dependencies
deployment
detchnical debt
discussion
docker
documentation
donations
duplicate
enhancement
feature request
frontend
fundraising
good first issue
good issue
help wanted
high
implemented
important
improvement
incomplete
invalid
investigation
kubernetes
low
low impact
medium
medium
medium impact
migration from 2.0
migration from 2.1
missing-language
missing-ocr-language
no-activity
note
ocr
outofscope
packaging
performance
popular request
pull-request
pypi
question
raspberry pi
roadmap
search
security
setup
status
task
technical debt
updates
user xp
version 1.4.0 - demo
will be implemented
will not be implemented
wontfix
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference
starred/papermerge#219
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @omemishra on GitHub (Dec 25, 2020).
Original GitHub issue: https://github.com/ciur/papermerge/issues/271
Originally assigned to: @ciur on GitHub.
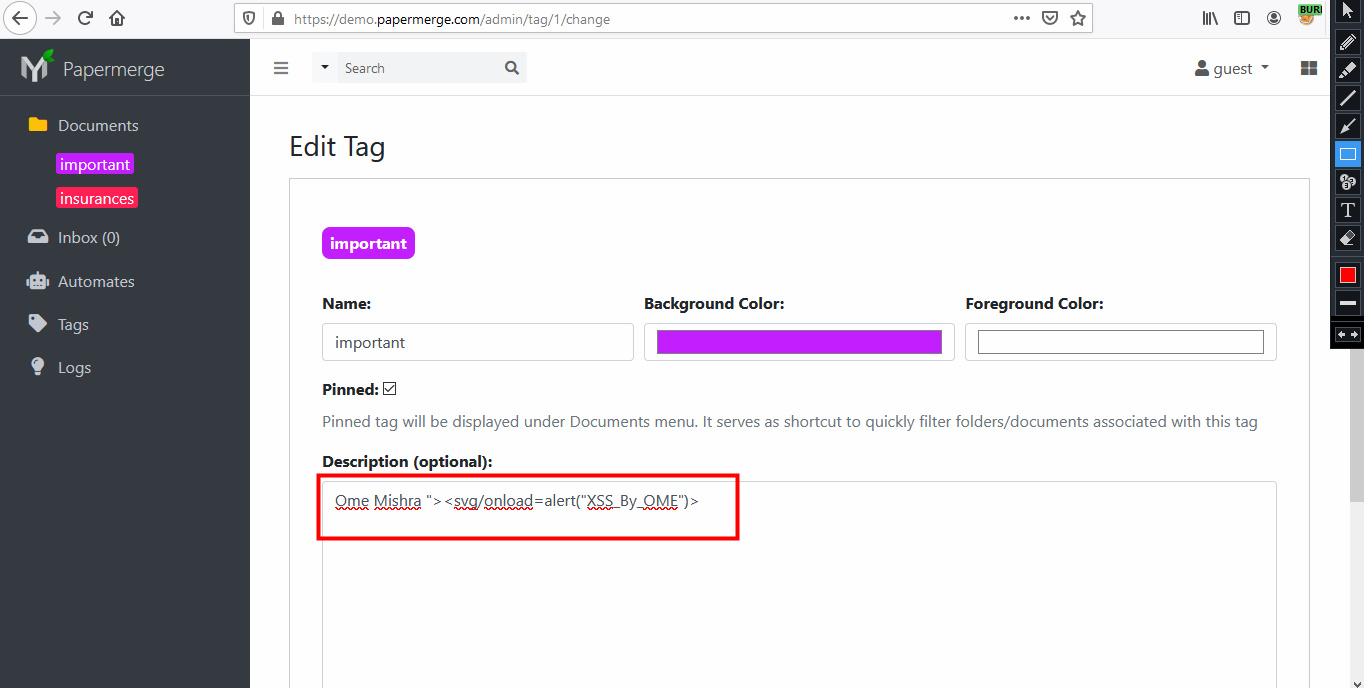
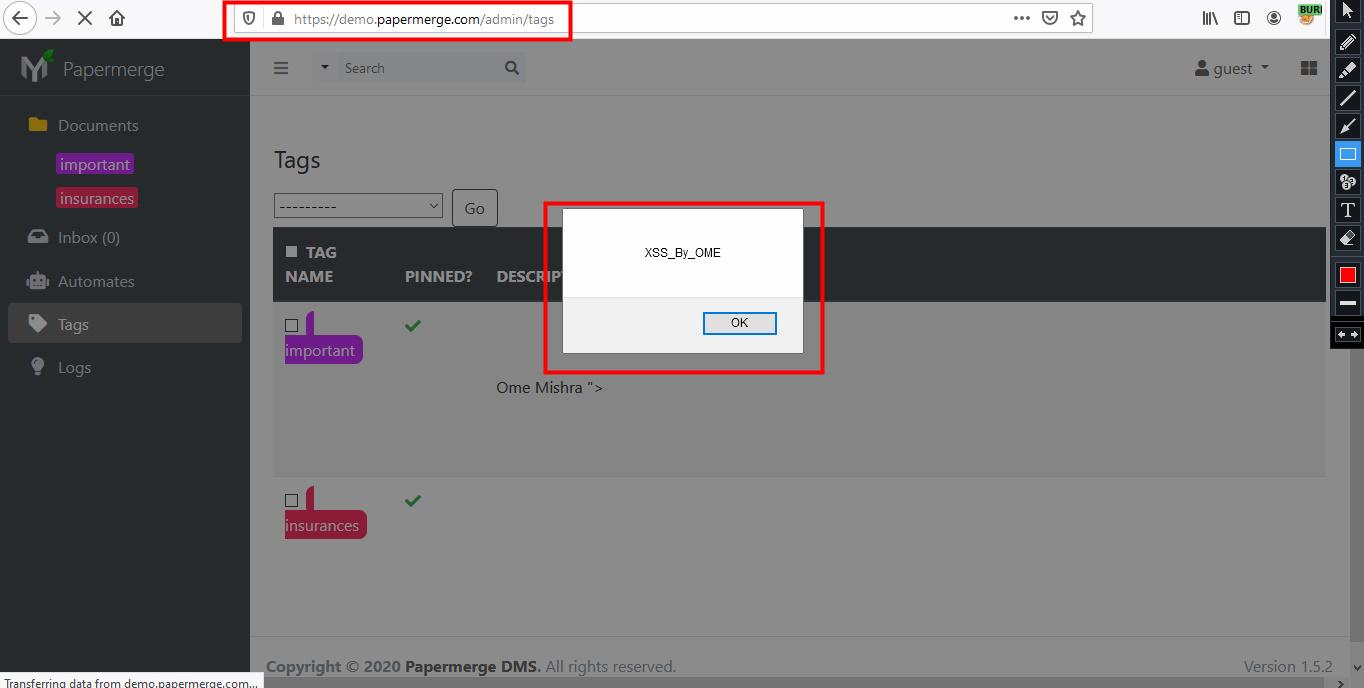
Dear Team,
Hope you are doing very well, i was looking into the application and i find that i can access to guest option so i was checking your application and i find a stored cross site scripting on Tags option.
Steps:-
Impacts:-
Adding POC down below
Thanks & Regards
Ome
@ciur commented on GitHub (Dec 26, 2020):
@omemishra, thank you for your security audit. I will fix this issue.
@ciur commented on GitHub (Dec 27, 2020):
Fixed in 1.5.x branch.
Fix is available as part of 1.5.5 release.
This is actually a bug in Django :), it does not escape form input in case of
form.save(commit=False)@omemishra commented on GitHub (Dec 27, 2020):
Dear Ciur,
Thank you so much for your response , please let me know when it will be fixed so that i can recheck it again.
Regards
Ome
@omemishra commented on GitHub (Jan 4, 2021):
Dear Team,
Let me know if this vulnerability is fixed?
Regards
Ome
@ciur commented on GitHub (Jan 4, 2021):
@omemishra, yes it is fixed in latest release (which is 1.5.5)
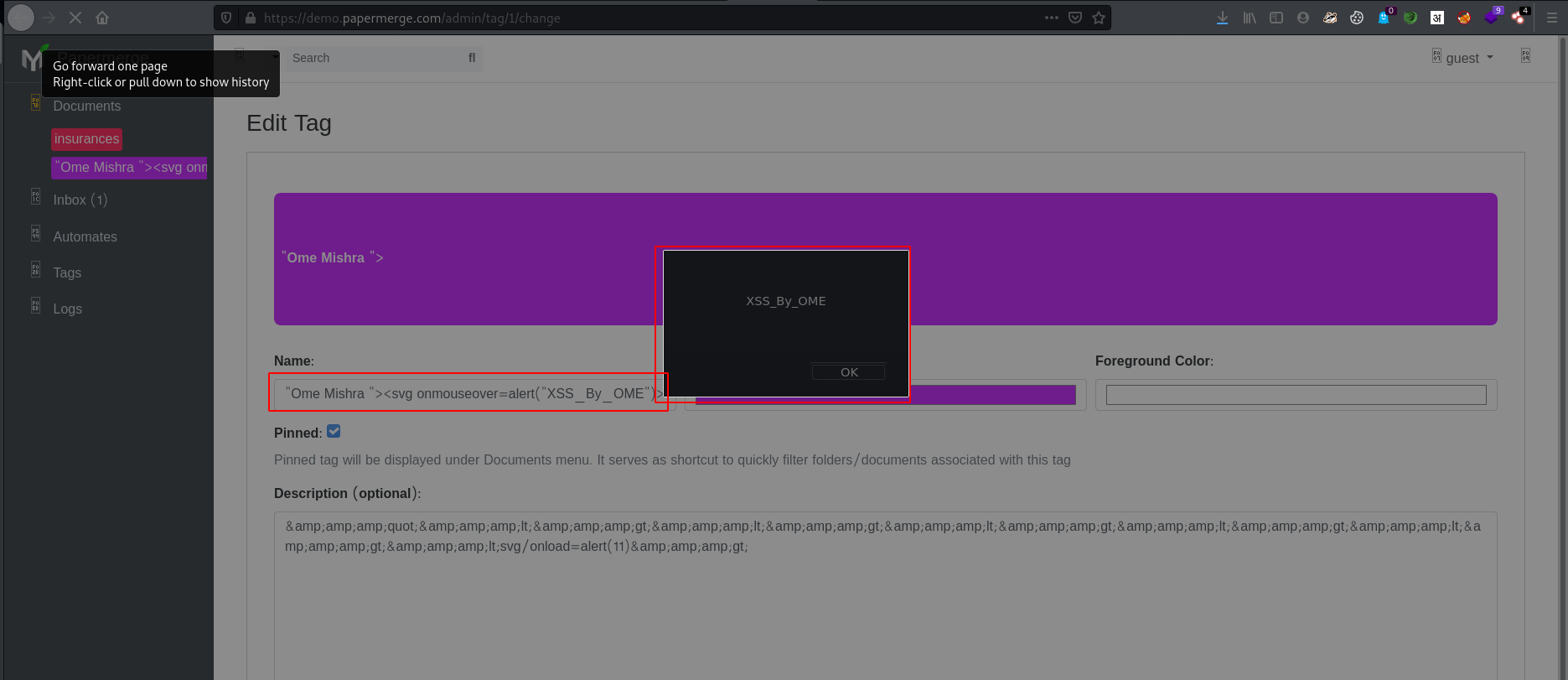
@omemishra commented on GitHub (Jan 4, 2021):
Dear team,
Again i have found the xss
Steps:-
Look like this is not yet fixed...
Regards
Ome
@ciur commented on GitHub (Jan 6, 2021):
@omemishra, thanks for feedback!
Will be fixed!
@omemishra commented on GitHub (Jan 6, 2021):
Hello Team,
Thanks for your response.
Let me know when it will be fixed.
Regards
Ome
@ciur commented on GitHub (Feb 2, 2021):
@omemishra, fixed. You can check it directly on https://demo.papermerge.com
Credentials are guest/password77a (they are public, as guest account is used for public demo)
@omemishra commented on GitHub (Feb 2, 2021):
Dear @ciur,
thanks for your response i have found more XSS on this application hope there is any bug bounty. hahaha
link:-
https://demo.papermerge.com/document/26/
in images metadata add "Ome Mishra "><svg onmouseover=alert("XSS_By_OME")>" and you will see the XSS payload executed successfully
link 2 :
https://demo.papermerge.com/
in folder metadata add "Ome Mishra "><svg onmouseover=alert("XSS_By_OME")>" and you will see the XSS payload executed successfully
Also please add client side validation as well because self xss is there on previously reported place.
Regards
Ome
@ciur commented on GitHub (Feb 3, 2021):
@omemishra, at this point there are no bug bounties. The best thing I can do at this moment is to add you to contributors list as security auditor.
I fixed XSS issue for metadata. Demo page features latest code updates (of the master branch).
Thank you for your great help!
@omemishra commented on GitHub (Feb 6, 2021):
Dear Ciur,
Thanks for adding me in contributor list.
We can test your whole website like VAPT, Please share your email if you want a proper VAPT.
Thanks & Regards
Ome