mirror of
https://github.com/ciur/papermerge.git
synced 2026-04-25 12:05:58 +03:00
[GH-ISSUE #228] Stored Cross-Site Scripting (XSS) #181
Labels
No labels
2.1
3.0
3.0.1
3.0.2
3.0.3
3.0.3
3.1
3.2
3.2
3.3
3.5
3.x
Fixed. Waiting for feedback.
Fixed. Waiting for feedback.
UX
Version 2.1 - alpha
XSS
announcement
beta
blocker
bug
cannot reproduce
confirmed
confirmed
critical
demo
dependencies
deployment
detchnical debt
discussion
docker
documentation
donations
duplicate
enhancement
feature request
frontend
fundraising
good first issue
good issue
help wanted
high
implemented
important
improvement
incomplete
invalid
investigation
kubernetes
low
low impact
medium
medium
medium impact
migration from 2.0
migration from 2.1
missing-language
missing-ocr-language
no-activity
note
ocr
outofscope
packaging
performance
popular request
pull-request
pypi
question
raspberry pi
roadmap
search
security
setup
status
task
technical debt
updates
user xp
version 1.4.0 - demo
will be implemented
will not be implemented
wontfix
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference
starred/papermerge#181
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @l4rm4nd on GitHub (Nov 27, 2020).
Original GitHub issue: https://github.com/ciur/papermerge/issues/228
Originally assigned to: @ciur on GitHub.
Description
Improper validation of user input leads to stored cross-site scripting (XSS) or HTML injection in the papermerge web application. If a user inserts JavaScript or HTML code into a folder name, the specified payload will be executed on opening the folder.
Expected
Specifying potentially malicious client side code should not be executed in the web application by the browser.
Actual
The browser successfully executes the specified JS or HTML payloads if the newly created folder is opened.
Steps to reproduce
Impact
This may allow an attacker to steal sensitive session information or CSRF tokens for executing a Cross-Site Request Forgery attack.
Likelihood
Authentication is required to access the papermerge web application.
Recommendation
Do not trust any user input and validate inputs properly. See https://owasp.org/www-community/attacks/xss/
Info:
Tested in the publicly available demo page. https://demo.papermerge.com/admin/browse
@l4rm4nd commented on GitHub (Nov 27, 2020):
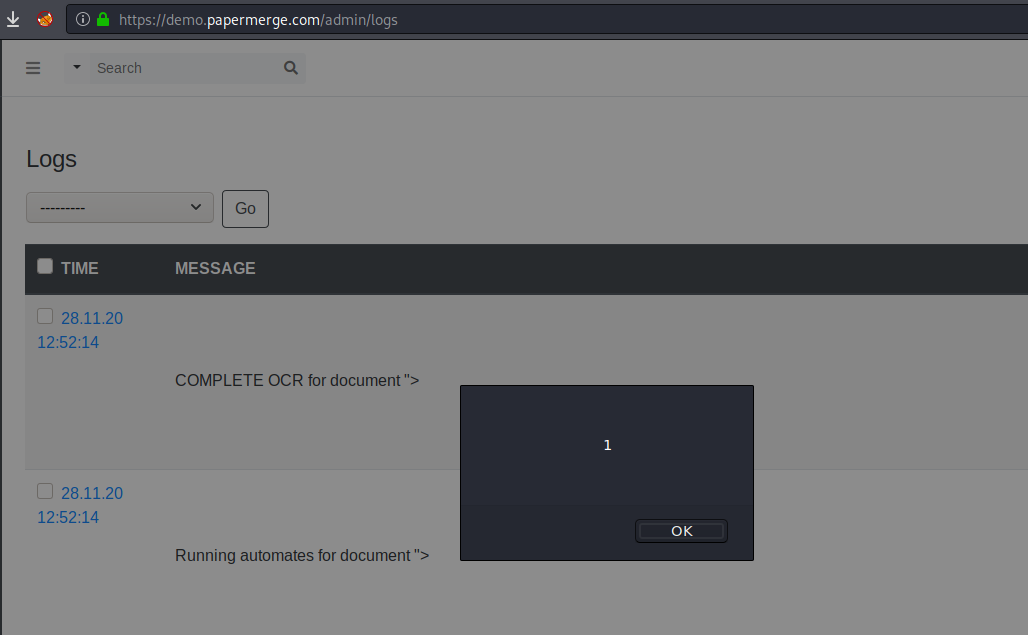
Just a quick proof of concept:
@ciur commented on GitHub (Nov 28, 2020):
@l4rm4nd, really good one! Thank you for opening this security issue. I will fix it and ship it as part of 1.5.1 release.
Thank you!
@l4rm4nd commented on GitHub (Nov 28, 2020):
BTW, this also works for uploaded file names.
Steps to reproduce
"><svg onload=alert(1)>.pngProof of concept
XSS PNG file uploaded in a "Test" folder of the demo papermerge webpage.
https://demo.papermerge.com/admin/browse#19
@l4rm4nd commented on GitHub (Nov 28, 2020):
Payloads are also reflected in the logs area https://demo.papermerge.com/admin/logs
@ciur commented on GitHub (Nov 28, 2020):
@l4rm4nd, oh, man, thank you for your security audit. I will fix issues in following days and release 1.5.1 with those security fixes.
Thanks again!
@l4rm4nd commented on GitHub (Nov 28, 2020):
Sure, no worries! Thanks for your fast replies and the will to fix the issues.
BTW, tags are also susceptible to XSS.
Steps to reproduce
@ciur commented on GitHub (Nov 29, 2020):
fixes for XSS issues so far (work in progress):
@ciur commented on GitHub (Nov 29, 2020):
@l4rm4nd
I released 1.5.1 which contains bug fixes plus partial fixing of this XSS - this is why current issue #228 is referenced in that release.
However fixing all XSS vector attacks requires significantly more changes.
Complete fix for XSS problems will be provided as part of 1.5.2. Release 1.5.2 will be entirely dedicated to XSS problems.
It will be out in a week.
Thank you again for your detailed audit!
@l4rm4nd commented on GitHub (Nov 29, 2020):
Catching and preventing malicious user input such as XSS payloads with a custom regex might work, but is not complete.
I'm not an expert in Django but I remember some built-in escaping functions such as
escape()andconditional_escape()which could be used.from django.utils.html import escapeBut I will also test some stuff after your fix release.
@ciur commented on GitHub (Nov 30, 2020):
@l4rm4nd, right! I added in several places escape(...) before saving to database.
Release which fixes above mentioned issues is 1.5.2
@l4rm4nd commented on GitHub (Dec 3, 2020):
Identified XSS vectors mitigated by release 1.5.2