mirror of
https://github.com/NginxProxyManager/nginx-proxy-manager.git
synced 2026-04-25 09:25:55 +03:00
[GH-ISSUE #919] AccessList Has Stopped Working After Switching From Flexible SSL to Full (Strict) SSL on CloudFlare #778
Labels
No labels
awaiting feedback
bug
cannot reproduce
dns provider request
duplicate
enhancement
enhancement
enhancement
good first issue
help wanted
invalid
need more info
no certbot plugin available
product-support
pull-request
question
stale
troll
upstream issue
v2
v2
v2
v3
wontfix
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference
starred/nginx-proxy-manager-NginxProxyManager#778
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @jfl1616 on GitHub (Mar 1, 2021).
Original GitHub issue: https://github.com/NginxProxyManager/nginx-proxy-manager/issues/919
I'm unable to post on Ngninx Proxy Manager reddit due to the restricted user.
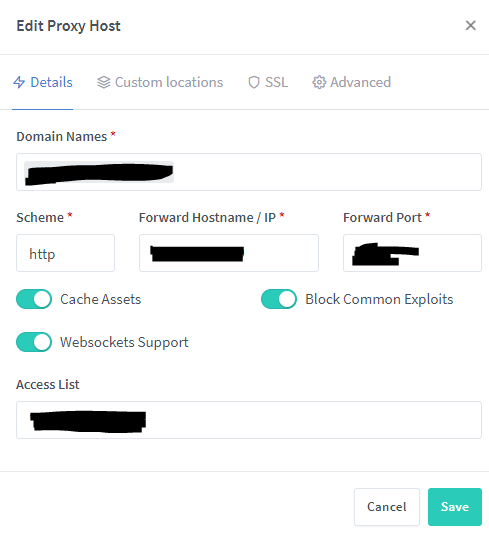
Describe the bug
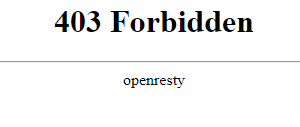
I'm currently experiencing the issue on Nginx Proxy Manager with Access Lists function right after I changed the Cloudflare SSL options. I realized that I've received the warning about exposing my origin IP address via DNS records on the multiple sub-domains on Cloudflare. I changed these sub-domains to be proxied in order to protect my origin IP address. However, it creates a different issue when I tried to visit my domain that shows the error message (ERR_TOO_MANY_REDIRECTS). I resolved this issue by switching from Flexible SSL to Full(Strict) SSL on CloudFlare. I'm currently seeing the page "Forbidden 403 error" when I enable the access list with my own public IP address. I just checked the proxy_host log to see the specific visitor IP, myself, and noticed that it shows different IP address, instead of my Public IP (Cloudflare's IP address's effect on it). I've been researching on this one, it seems that I will need to restore original visitor IPs in this case.
Version of Nginx Proxy Manager
Expected behavior
NGNIX Proxy Manager should be able to detect the original visitor IPs in order to match the specific IP address on Access List configuration.
Operating System
Screenshots
@apainter2 commented on GitHub (Jun 1, 2021):
This is how Cloudflare is supposed to work, if you have Proxied-DNS enabled.
Just had the same issue myself, and here is my solution.
As NPM can not see your actual IP address, it sees the Cloudflare proxied IP address. You need to use the Advanced option for the proxy host and enter the following:
You can find the latest Cloudflare IP addresses via: https://www.cloudflare.com/en-gb/ips/
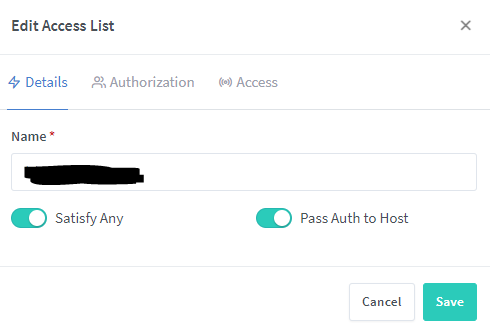
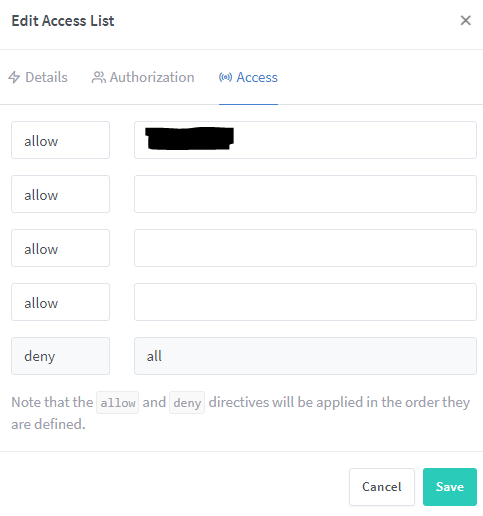
You can then use the Access ACL option to only permit your home router IP for example and then it works:
Only potential problem for the future is when Cloudflare updates their IP addresses, your list will be out of date. Maybe incorporate this into NPM?
Source: https://support.cloudflare.com/hc/en-us/articles/200170786-Restoring-original-visitor-IPs
Additional Info: https://danielmiessler.com/blog/getting-real-ip-addresses-using-cloudflare-nginx-and-varnish/
@NajibNour commented on GitHub (Jun 3, 2021):
@apainter2 I've given this a shot multiple times and it still does not work. also, you do not need to pull the ips yourself as NPM does it for you It fou look in the logs on boot up it does log it pulling Cloudflare ip's. The ips can be found in this file of the NPM container : /etc/nginx/conf.d/include/ip_ranges.conf
@NajibNour commented on GitHub (Jun 3, 2021):
@apainter2 did you have to put anything in the advanced section of your host? Also what version of NPM are you using?
@apainter2 commented on GitHub (Jun 3, 2021):
@NajibNour your right those IP ranges are in the file you linked.
So, yes I have placed the following into the advanced section of my proxy-host for it to pass on the proper visitor IP address to allow the ACL to work when using cloudflare:
real_ip_header CF-Connecting-IP;Oh, and I am using version 2.9.3 (latest at the time of this post).
@NajibNour commented on GitHub (Jun 3, 2021):
@apainter2 hmm I’ve given that a shot previously, but I have not had any luck. Where did you place the file for the ips and what where it’s contents?
@apainter2 commented on GitHub (Jun 3, 2021):
@NajibNour the list of Cloudflare IPs? I've left them where you referenced them, and only added the above-advanced option to the Advanced section.
The CF IPs are pre-populated within the /etc/nginx/conf.d/include/ip_ranges.conf file
You can verify by connecting to the container
docker exec -it name-of-npm-container /bin/bashonce connected to the container:
cat /etc/nginx/conf.d/include/ip_ranges.conf@NajibNour commented on GitHub (Jun 3, 2021):
@apainter2 yhea I figured just thought I would ask to be safe. The real ip header does not work for me. I will have to do some investigating. How to you view current established connection ip’s from within the NPM container? I’ve noticed there’s allot of tools that are not installed to view connected ips
@apainter2 commented on GitHub (Jun 3, 2021):
@NajibNour I list out the contents of the proxy-hosts ngnix access log:
within the NPM data directory which you mapped, in my instance as an example:
tail -f /home/USER/docker_files/npm/data/logs/proxy_host-XX.log
XX is the number linked to your proxy-host entry in the GUI.
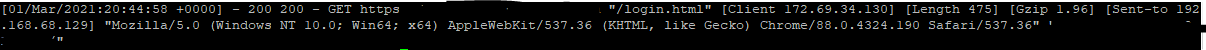
In my case a real-world example, with the
real_ip_header CF-Connecting-IP;set[03/Jun/2021:20:47:28 +0000] - 200 200 - GET https meh.example.domain.tld "/login" [Client 92.40.192.102] [Length 3533] [Gzip -] [Sent-to 192.168.1.9] "Mozilla/5.0 (iPhone; CPU iPhone OS 14_6 like Mac OS X) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/14.1.1 Mobile/15E148 Safari/604.1" "-"So, 92.40.192.102 is my mobile phone providers IP block range.
and without
real_ip_header CF-Connecting-IP;set:[03/Jun/2021:20:49:46 +0000] - 200 200 - GET https meh.example.domain.tld "/login" [Client 141.101.105.125] [Length 3541] [Gzip -] [Sent-to 192.168.1.9] "Mozilla/5.0 (iPhone; CPU iPhone OS 14_6 like Mac OS X) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/14.1.1 Mobile/15E148 Safari/604.1" "-"Where as 141.101.105.125 is: one of Cloudflares proxy IP addresses.
@NajibNour commented on GitHub (Jun 3, 2021):
@apainter2 Thanks for this. I've just given it shot. It does show the proper Ip address in the logs. the following does work "real_ip_header CF-Connecting-IP;"
But access lists are still an issue. I have created an access list with my ip address as allow and everything else as deny and it is set to satisfy any. I still get returned a 403. Logs it shows up as 403 as well.
@NajibNour commented on GitHub (Jun 3, 2021):
Please Disregard, ACL's Do work it's just a little finicky. You must have the host enabled, Create the ACL, Then set the ACL then Unset then set The ACL. That was the only way I could get it to work.
@phgoff commented on GitHub (Jan 30, 2022):
This is solved my problem. Thank you.
@github-actions[bot] commented on GitHub (Mar 18, 2024):
Issue is now considered stale. If you want to keep it open, please comment 👍
@github-actions[bot] commented on GitHub (Apr 29, 2025):
Issue was closed due to inactivity.