mirror of
https://github.com/NginxProxyManager/nginx-proxy-manager.git
synced 2026-04-25 01:15:51 +03:00
[GH-ISSUE #646] Running non-ssl protocols over ssl port (i.e. using SSH over Nginx using $ssl_preread_protocol ) #549
Labels
No labels
awaiting feedback
bug
cannot reproduce
dns provider request
duplicate
enhancement
enhancement
enhancement
good first issue
help wanted
invalid
need more info
no certbot plugin available
product-support
pull-request
question
stale
troll
upstream issue
v2
v2
v2
v3
wontfix
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference
starred/nginx-proxy-manager-NginxProxyManager#549
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @maltokyo on GitHub (Oct 10, 2020).
Original GitHub issue: https://github.com/NginxProxyManager/nginx-proxy-manager/issues/646
This article describes exactly what I want to do:
https://www.nginx.com/blog/running-non-ssl-protocols-over-ssl-port-nginx-1-15-2/
Basically, for one of my domain names (vhost), I would like port 443 to be accepted and redirect connections to my SSH server, rather than a http/https service.
The code to do it is in the article and pasted below (checks if the 443 packets are destined for https or SSH and redirects accordingly, but I am unsure where to insert this or how to use it with NPM). Could someone please give me a hint, what I would need to do to get this working for just one domain name?
Any advice or help would be really appreciated.
@maltokyo commented on GitHub (Oct 10, 2020):
At first it seems that NPM can do this with "Add Stream" (in this section):
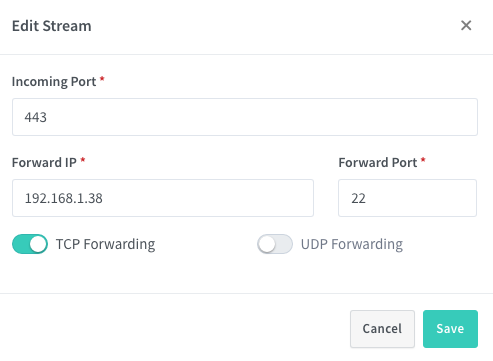
However, the implementation here seems to NOT use $ssl_preread_protocol - so if there is another service already listening on 443, the above does not work. So it leaves a couple more questions:
@litio2001 commented on GitHub (Jun 8, 2021):
I think your query is related precisely to this issue that I just read. #344
@github-actions[bot] commented on GitHub (Mar 24, 2024):
Issue is now considered stale. If you want to keep it open, please comment 👍
@maltokyo commented on GitHub (Mar 24, 2024):
Any help from anyone?
@litio2001 commented on GitHub (Mar 28, 2024):
Have you tried the alternative mentioned here?: #344
Due to lack of time I have not been able to try it.
@github-actions[bot] commented on GitHub (Dec 18, 2024):
Issue is now considered stale. If you want to keep it open, please comment 👍
@maltokyo commented on GitHub (Dec 18, 2024):
Bump
On Wed, Dec 18, 2024, 3:06 AM github-actions[bot] @.***>
wrote:
@albeec13 commented on GitHub (Jan 24, 2025):
@maltokyo I'm pretty sure you can make this work by using this method: https://nginxproxymanager.com/advanced-config/#custom-nginx-configurations
Essentially, create a
/data/nginx/custom/directory in your NPM docker data directory if it doesn't already exist, then create a file called/data/nginx/custom/stream.confand paste the contents of yourstreamdirective in there, without the outerstreamblock, something like:There is a caveat, however, which is this will only work if you have nothing else listening on port 443, meaning if you have any standard proxy hosts assigned to HTTPS, this will conflict and cause NPM to complain about 0.0.0.0:443 already being bound at startup.
Unfortunately, NPM doesn't allow you to set the incoming port for proxy hosts, as the only options are HTTP/HTTPS from the "scheme" dropdown box. Therefore, you can't forward to a different internal port from the stream directive which is already listening on 443.
There is a way to do this using a standard nginx install, if you choose to go that route, but you'll lose the pretty GUI of NPM and the built-in SSL cert renewal functionality. For example, I have a setup similar to this running on a standard non-NPM nginx install on a linux server, and what I did there was something like this:
In this case, the stream listens to port 443, and uses
ssl_preread_protocolto determine whether it's TLS (I only check for 1.2 or 1.3, as the others are deprecated and I don't allow them to be used, but change this to your preference), and if it does not return a TLS version, it assumes it's an SSH connection.Notice, the upstreams are both using localhost (127.0.0.1). The ssh server, is the same machine as the nginx service, but running on port 12345, while all other HTTPS requests are forwarded back to the same machine via localhost, but using port 444, which is not exposed beyond the firewall. However, all subsequent HTTPS directives in my nginx.conf look to port 444 instead of 443, like so:
In other words, a request from a public IP would go like this:
More details here: https://blog.thewalr.us/2019/04/05/using-nginx-stream-directive-to-host-ssh-and-multiple-https-servers-on-the-same-port/
@github-actions[bot] commented on GitHub (Nov 11, 2025):
Issue is now considered stale. If you want to keep it open, please comment 👍