mirror of
https://github.com/NginxProxyManager/nginx-proxy-manager.git
synced 2026-04-25 09:25:55 +03:00
[GH-ISSUE #2750] nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied) #1888
Labels
No labels
awaiting feedback
bug
cannot reproduce
dns provider request
duplicate
enhancement
enhancement
enhancement
good first issue
help wanted
invalid
need more info
no certbot plugin available
product-support
pull-request
question
stale
troll
upstream issue
v2
v2
v2
v3
wontfix
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference
starred/nginx-proxy-manager-NginxProxyManager#1888
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @maz1987in on GitHub (Mar 27, 2023).
Original GitHub issue: https://github.com/NginxProxyManager/nginx-proxy-manager/issues/2750
Checklist
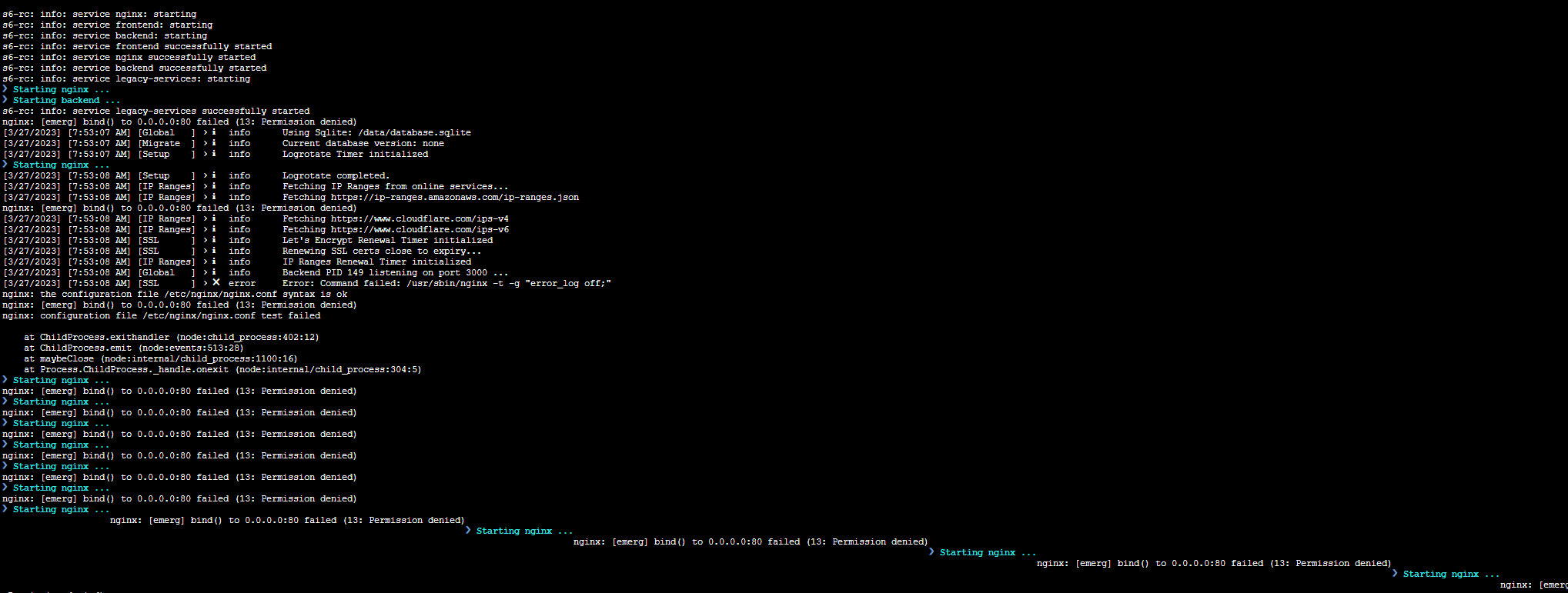
jc21/nginx-proxy-manager:latestdocker image?Describe the bug
when I upgrade to the latest "2.10.0" I got
Nginx Proxy Manager Version
To Reproduce
Run docker with option "network_mode: host"
Expected behavior
Screenshots
Operating System
QNAP NAS
Additional context
@pmoon00 commented on GitHub (Mar 27, 2023):
Can confirm I'm seeing the exact same issue with the same configuration. Have rolled back to 2.9.22 to temporarily resolve the issue.
@kilrah commented on GitHub (Mar 27, 2023):
Same on Unraid with Host network.
@hdavid0510 commented on GitHub (Mar 27, 2023):
Can confirm, exact same issue. I also reverted back to 2.9.22.
(edit) Changed host network to bridge, to bypass the issue. No other configuration changed. Since NPM config I'm using does not serve high load, I'm going to stick with bridge network for now.
@jsuelwald commented on GitHub (Mar 27, 2023):
I've got the same problem since the update
@psychogun commented on GitHub (Mar 27, 2023):
Same. Using podman on Rocky Linux.
@kahn2k commented on GitHub (Mar 27, 2023):
Same problem running docker on Synology, with portainer and watchtower.
Have been on bridge network without problems before this update.
Reverted back to 2.9.22 and problem resolved.
@functionaldude commented on GitHub (Mar 27, 2023):
Same issue running docker on Synology, DSM 7.1.1-42962
The container is in a bridge network
@wzzrd commented on GitHub (Mar 27, 2023):
Yup, same: running with podman on RHEL9
@azchoi commented on GitHub (Mar 27, 2023):
Same here!!!!
[Synology DSM 7.1] npm docker log
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
@steindorarnar commented on GitHub (Mar 27, 2023):
Same here, reverted to 2.9.22
Synology, docker, portainer, watchtower.
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
@zsmbrvr commented on GitHub (Mar 27, 2023):
I used
to revert to 2.9.22.
@stephanvierkant commented on GitHub (Mar 27, 2023):
Please don't comment with just 'same here!'. I think it's clear that there is an issue with the latest release.
@CelticWebSolutions commented on GitHub (Mar 27, 2023):
Same issue here running on Synology with bridge networking. Unfortunately I spent a long time attempting to debug why it coudn’t bind to the port. Stop the container and port 80 became free, start the container at the port is in use via docker-proxy but NPM fails to bind to it.
After deleting everything and attempting to start again, I found it was still the same, permission denied when binding the port. Checked and spotted there’d been a recent update,
Rolling back to 2.9.22 fixes the issue For the time being.
Just realised @stephanvierkant had already mentioned using older release as I had :)
@Candinya commented on GitHub (Mar 27, 2023):
It seems that since v2.10.0 the nginx is ran by
npmuserrather than default (root maybe?), whom might don't have sufficient permissions to listen on lower ports like 80 & 443. Not sure if this is the cause. 🤔See full changelogs here: https://github.com/NginxProxyManager/nginx-proxy-manager/compare/v2.9.22...v2.10.0
@florisdipt commented on GitHub (Mar 27, 2023):
Same isue here;running inside proxmox lcx container. my docker compose:
@redtripleAAA commented on GitHub (Mar 28, 2023):
Would be good to understand what causes the issue.
Same here with Synology DSM, running latest or 2 same issue.
But running image:
'jc21/nginx-proxy-manager:2.9.22'fixed the issue for now@zandhaas commented on GitHub (Mar 28, 2023):
I had this same issue when I tried to install the beta version of the 3.0. I did try to add the PUID and GUID of root but that did not solve the issue for version 3.
But then I thought this is still development so.........
But now I have this same issue with version 2.10
I'm running nginx_pm on my Synology.
@907739769 commented on GitHub (Mar 28, 2023):
problem solved please let me know thanks.
@zandhaas commented on GitHub (Mar 28, 2023):
Perhaps you or someone else can give us an update on what is going on to solve this issue instead of giving us Thumb's down's
Something like: " we see there is an error and we are looking into it. We expect to have a solutions in xx days"
And by the way: I think I added some extra information by telling the communicty that I see this exact same error in the new version 3 NGINX-PM
@evanlabs commented on GitHub (Mar 28, 2023):
I tried to test on CentOS 7 and Debian 10/11, this problem only happens on CentOS 7 system, not on Debian.
Maybe because of npmuser permissions, just guessing.
source: docker/rootfs/etc/s6-overlay/s6-rc.d/prepare/10-npmuser.sh
@florisdipt commented on GitHub (Mar 28, 2023):
Are you talking about running directly inside the system without docker? Because i'm running debian + docker and still encountered the issue.
@evanlabs commented on GitHub (Mar 28, 2023):
Sorry, did not provide complete information.
I use docker to do npm testing on centos and debian.
@Jojonintendo commented on GitHub (Mar 28, 2023):
The release notes mention this:
Users running 2.10.0 won't be able to run this container rootless apparently (as I've been doint with podman). Otherwise this message appears:
And the container stops. Problem is, even when specifying PUID and PGID, the container shows the errors reported in this thread.
Maybe I don't understand well what the new configuration should be, based on the release notes. If running the container as root is now a requisite, that would be a shame for us rootless users.
Any pointers would be greatly appreciated.
@evanlabs commented on GitHub (Mar 28, 2023):
I tried to modify the following s6 startup script, but it still didn't solve the problem
source: docker/rootfs/etc/s6-overlay/s6-rc.d/nginx/run
'exec s6-setuidgid npmuser nginx' => 'exec nginx'
@BobWs commented on GitHub (Mar 28, 2023):
Same problem running docker on Synology DSM 7.1.1 with Portainer.
Reverted back to 2.9.22 and problem resolved.
@Nazgile94 commented on GitHub (Mar 28, 2023):
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
same ubuntu 22.x
@gabeosx commented on GitHub (Mar 29, 2023):
Same issue
@Trolann commented on GitHub (Mar 29, 2023):
This seems to be expected behavior. @maz1987in @Jojonintendo @Candinya @evanlabs
Release notes for 2.9.22 state:
https://github.com/NginxProxyManager/nginx-proxy-manager/releases
and
But I can't find anything about how to prevent this 'adverse affect'.
Copied my comment above from #2761 which appears to be the duplicate
@Jojonintendo commented on GitHub (Mar 29, 2023):
Same issue with the new image 2.10.1
I've tested the same as my previous comment, with PUID and PGID, and without them. The issue persists.
I've also tried running the container with sudo, to no avail. So it doesn't seem to be only related to rootless containers.
@azchoi commented on GitHub (Mar 29, 2023):
Right, I also tried to install 2.10.1 to Synology 7.1.1, the result was same as before. Only 2.9.22 is the best way to me.
@jurjen74 commented on GitHub (Mar 29, 2023):
Same here on Synology. Latest (2.10.1) is not working. Rolled back to 2.9.22
@nemccarthy commented on GitHub (Mar 29, 2023):
Having the same issue with this. I suspect the issue is related to the s6 change and this line in nginx config https://github.com/NginxProxyManager/nginx-proxy-manager/compare/v2.9.22...v2.10.0#diff-45b340b2ff6f4d041ae1aad210aaa0cd31b41139574725ef971a38fab076caa4L4
The issue is not just the
NET_BIND_SERVICEcapability missing from the docker run, its a simple issue with the container itself. A non-root user cannot bind to ports less than1024. This docker file should give the newnpmuserpermissions to do this.If you are seeing
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)I have found the following to work...Temporary solution (without rollback):
bash> Okapt updateapt install libcap2-binsetcap 'cap_net_bind_service=+ep' /usr/sbin/nginxYou should now see nginx proxy manager successfully start! No need to restart the container. The issue with this fix is that if you have something like watchtower running you will lose this on next update until its fixed in the offical docker image.
Good hygine would also be to add the
PUIDandPGIDenv vars to a non-root user that lives on your system.Suggested Proper Fix:
Note that the above is NOT reccomended as a permanent fix, and shouldn't be raised as a PR in the Dockerfile (as it adds portability and security issues - e.g. PSP violations in a locked down k8s cluster).
IMHO, the proper fix will be to move all NPM binds to a different set of ports like 8080... This is probably a bigger change given the config generation. One can bind 80 on their network interfaces to 8080 in the container (i.e.
docker run -p 80:8080 ...) so you get the behaviour you need... This avoids the need for elevated privileges, since non-root users can bind to ports higher than 1024 and the only way I know how to get this working...For reference on Synology:

@florisdipt commented on GitHub (Mar 29, 2023):
If Semantic Versioning is respected, this shouldn't be expected behaviour as this is a minor version not a major therefor it shouldn't break compatibility.
Obviously backing up al configuration before changing versions is a good idea, as one could never have enough backups only too little hard drive space ;)
On Another note I see a bugfix version for 2.10 was issued 11 hours ago. But replies so far in this issue seem to indicate that is not a fix for this issue
@TarekMSayed commented on GitHub (Mar 29, 2023):
2.9.22 works for me too but I noticed the versions latest, 2, or 2.10 creates files with UID=GID=911 while 2.9.22 use root user


@Trolann commented on GitHub (Mar 29, 2023):
@florisdipt completely agree, and there should be release notes clearly showing how to correct it. I gave the installation instructions a glance and couldn't see updates there but in off on vacation today so couldn't dig in.
@coalfield commented on GitHub (Mar 30, 2023):
thanks for your fix it works and greatly appreciated!! Do you know what permissions this use would need for synology, is it worth creating a specific user for this, and would be keen to know the minimal permissions they would need to allow them to be used with the container?
@nemccarthy commented on GitHub (Mar 30, 2023):
PUID (Process User ID) and PGID (Process Group ID) so as you know they are environment variables used in Docker containers to set the user and group IDs for the container's processes. They help to manage file and folder permissions for the data shared between the host system and the container - in this case the data folder and cert folder volume mounts for NPM.
I generally create a basic user with no login via the control panel in the Synology NAS that only has access to a volume for my docker containers. I create a user for each domain set of containers say user
docker-npm, I think give this user ownership permissions to a docker-npm folder in the NAS where I want to mount volumes in the container.Once you create a new user, to get the User ID and Group ID on the NAS the easiest way is to create a Task from control panel and add the following command to the steps

cat /etc/passwdyou should then be able to manually run the task by hitting Run on the list of tasks and view the output (Action > View Result) which show you the user name you create along with the UID and GID.@apriliars3 commented on GitHub (Mar 30, 2023):
Works
I have PUID and PGID with my user on docker. Why not works with this?
docker run -d --name=nginx_proxy_manager
-p 8880:80
-p 81:81
-p 4443:443
-e PUID=1026
-e PGID=100
-e TZ=Europe/Madrid
-v /volume1/docker/npm/config.json:/app/config/production.json
-v /volume1/docker/npm/data:/data
-v /volume1/docker/npm/letsencrypt:/etc/letsencrypt
--restart always
jc21/nginx-proxy-manager
@coalfield commented on GitHub (Mar 30, 2023):
Thanks that's good advice I have taken, although its functioning OK I am getting:
Didn't notice this error before do you know if there is a way to move the paths that cannot be accessed to within the writable docker folder for example?
@evanlabs commented on GitHub (Mar 31, 2023):
This problem has been solved in the v2.10.2 version, and I tested the docker container on CentOS and Debian without any problems.
Thanks to the developer for fixing this issue quickly.
@ituri commented on GitHub (Mar 31, 2023):
What do I need to change on a system that has been working fine up until this recent bug? I'm already on v2.10.2 but it's not working yet.
Still getting this:
s6-rc: info: service s6rc-oneshot-runner: starting s6-rc: info: service s6rc-oneshot-runner successfully started s6-rc: info: service fix-attrs: starting s6-rc: info: service fix-attrs successfully started s6-rc: info: service legacy-cont-init: starting s6-rc: info: service legacy-cont-init successfully started s6-rc: info: service prepare: starting ❯ Configuring npmuser ... id: 'npmuser': no such user ❯ Checking paths ... ❯ Setting ownership ... s6-rc: fatal: timed out /run/s6/basedir/scripts/rc.init: warning: s6-rc failed to properly bring all the services up! Check your logs (in /run/uncaught-logs/current if you have in-container logging) for more information. s6-sudoc: fatal: unable to get exit status from server: Operation timed out@zandhaas commented on GitHub (Mar 31, 2023):
I also have the same issue as @ituri has.
I running the nginx-pm on my Synology
Returned to v 2.9.22 again
@azchoi commented on GitHub (Mar 31, 2023):
I've reinstall 2.10.2 to Synology 7.1.1 without PUID/PGID and issue has been solved.
Are you using PUID/PGID?
Here is my Log....
| \ | | _ | / |
| | | |) | |/| |
| |\ | __/| | | |
|| _|| || |_|
User ID: 0
Group ID: 0
s6-rc: info: service prepare successfully started
s6-rc: info: service nginx: starting
s6-rc: info: service frontend: starting
s6-rc: info: service backend: starting
s6-rc: info: service nginx successfully started
s6-rc: info: service frontend successfully started
s6-rc: info: service backend successfully started
s6-rc: info: service legacy-services: starting
❯ Starting nginx ...
❯ Starting backend ...
s6-rc: info: service legacy-services successfully started
@zandhaas commented on GitHub (Mar 31, 2023):
[3/31/2023] [9:54:38 AM] [Global ] › ℹ info Using MySQL configuration
❯ Starting nginx ...
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
❯ Starting nginx ...
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
❯ Starting nginx ...
[3/31/2023] [9:54:41 AM] [Migrate ] › ℹ info Current database version: 20211108145214
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
[3/31/2023] [9:54:41 AM] [Setup ] › ℹ info Logrotate Timer initialized
[3/31/2023] [9:54:41 AM] [Setup ] › ℹ info Logrotate completed.
[3/31/2023] [9:54:41 AM] [IP Ranges] › ℹ info Fetching IP Ranges from online services...
[3/31/2023] [9:54:41 AM] [IP Ranges] › ℹ info Fetching https://ip-ranges.amazonaws.com/ip-ranges.json
[3/31/2023] [9:54:41 AM] [IP Ranges] › ℹ info Fetching https://www.cloudflare.com/ips-v4
[3/31/2023] [9:54:41 AM] [IP Ranges] › ℹ info Fetching https://www.cloudflare.com/ips-v6
[3/31/2023] [9:54:41 AM] [SSL ] › ℹ info Let's Encrypt Renewal Timer initialized
[3/31/2023] [9:54:41 AM] [SSL ] › ℹ info Renewing SSL certs close to expiry...
[3/31/2023] [9:54:41 AM] [IP Ranges] › ℹ info IP Ranges Renewal Timer initialized
[3/31/2023] [9:54:41 AM] [Global ] › ℹ info Backend PID 168 listening on port 3000 ...
❯ Starting nginx ...
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
❯ Starting nginx ...
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
❯ Starting nginx ...
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
❯ Starting nginx ...
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
❯ Starting nginx ...
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
@azchoi commented on GitHub (Mar 31, 2023):
Here is my script for your reference.
version: "3.8"
services:
app:
image: 'jc21/nginx-proxy-manager:latest'
restart: unless-stopped
ports:
- '8080:80' # Public HTTP Port
- '8443:443' # Public HTTPS Port
- '81:81' # Admin Web Port
environment:
DB_MYSQL_HOST: "db_ip"
DB_MYSQL_PORT: 3306
DB_MYSQL_USER: "db_user_name"
DB_MYSQL_PASSWORD: "db_pw"
DB_MYSQL_NAME: "db_name"
TZ: Asia/Seoul # option
volumes:
- '/volume1/docker/npm/data:/data'
- '/volume1/docker/npm/letsencrypt:/etc/letsencrypt'
@zandhaas commented on GitHub (Mar 31, 2023):
Are you starting docker-compose as root user or as an other user??
I'm starting it as root user.
@azchoi commented on GitHub (Mar 31, 2023):
root.
sudo -i
docker-compose up -d
@zandhaas commented on GitHub (Mar 31, 2023):
That's what I do. The only difference is that I use a macvlan configuration so I using the original ports 80 and 443.
I try to intall a seperate test nginx-pm the way you have.
@zandhaas commented on GitHub (Mar 31, 2023):
Created a complete new nginx-pm container with corresponding DB.
Below my log
Enabling IPV6 in hosts in: /data/nginx
❯ Docker secrets ...
| \ | | _ | / |
| | | |) | |/| |
| |\ | __/| | | |
|| _|| || |_|
User UID: 911
User GID: 911
s6-rc: info: service prepare successfully started
s6-rc: info: service nginx: starting
s6-rc: info: service frontend: starting
s6-rc: info: service backend: starting
s6-rc: info: service frontend successfully started
❯ Starting nginx ...
s6-rc: info: service backend successfully started
❯ Starting backend ...
s6-rc: info: service nginx successfully started
s6-rc: info: service legacy-services: starting
s6-rc: info: service legacy-services successfully started
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
[3/31/2023] [10:15:27 AM] [Global ] › ℹ info Using MySQL configuration
[3/31/2023] [10:15:27 AM] [Global ] › ℹ info Creating a new JWT key pair...
❯ Starting nginx ...
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
❯ Starting nginx ...
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
❯ Starting nginx ...
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
❯ Starting nginx ...
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
❯ Starting nginx ...
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
❯ Starting nginx ...
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
❯ Starting nginx ...
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
❯ Starting nginx ...
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
[3/31/2023] [10:15:35 AM] [Global ] › ℹ info Wrote JWT key pair to config file: /data/keys.json
❯ Starting nginx ...
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
❯ Starting nginx ...
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
❯ Starting nginx ...
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
[3/31/2023] [10:15:38 AM] [Migrate ] › ℹ info Current database version: 20211108145214
❯ Starting nginx ...
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
[3/31/2023] [10:15:39 AM] [Setup ] › ℹ info Logrotate Timer initialized
[3/31/2023] [10:15:39 AM] [Setup ] › ℹ info Logrotate completed.
[3/31/2023] [10:15:39 AM] [IP Ranges] › ℹ info Fetching IP Ranges from online services...
[3/31/2023] [10:15:39 AM] [IP Ranges] › ℹ info Fetching https://ip-ranges.amazonaws.com/ip-ranges.json
[3/31/2023] [10:15:39 AM] [IP Ranges] › ℹ info Fetching https://www.cloudflare.com/ips-v4
[3/31/2023] [10:15:39 AM] [IP Ranges] › ℹ info Fetching https://www.cloudflare.com/ips-v6
[3/31/2023] [10:15:39 AM] [SSL ] › ℹ info Let's Encrypt Renewal Timer initialized
[3/31/2023] [10:15:39 AM] [SSL ] › ℹ info Renewing SSL certs close to expiry...
[3/31/2023] [10:15:39 AM] [IP Ranges] › ℹ info IP Ranges Renewal Timer initialized
[3/31/2023] [10:15:39 AM] [Global ] › ℹ info Backend PID 128 listening on port 3000 ...
❯ Starting nginx ...
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
❯ Starting nginx ...
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
[3/31/2023] [10:15:41 AM] [SSL ] › ✖ error Error: Command failed: /usr/sbin/nginx -t -g "error_log off;"
nginx: the configuration file /etc/nginx/nginx.conf syntax is ok
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
nginx: configuration file /etc/nginx/nginx.conf test failed
❯ Starting nginx ...
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
❯ Starting nginx ...
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
etc etc
@azchoi commented on GitHub (Mar 31, 2023):
BTW, below ID is different from me.
User ID: 0
Group ID: 0
@zandhaas commented on GitHub (Mar 31, 2023):
I know but with that same PUID and GUID version 2.9.22 is working as expected.
When I try to use PUID and GUID 0 (root) docker-compose says it's not a unique UID and thus nginx-pm does not start correctly.
So if some one has an idea on how to get version 2.10.x working that would be nice. I'm getting a bit frustrated because if this issue will not be resolved I have to think about moving to an other reverse proxy because all future development won't work in my environment.
@zandhaas commented on GitHub (Mar 31, 2023):
And when I use the version 2.9.22 for my fresh installed environment it's starting right away without an issue.
Very nice such an upgrade.
@ebildebil commented on GitHub (Mar 31, 2023):
Looking at your config, it seems that you are not using Host Networking?
I have 2 instances running, and the one that does not use host networking works fine.
When using host networking, i get the same errors.
The only way so far to solve host networking was to allow access to privileged ports to non root users. (as SUggested by nemccarthy earlier)
@apriliars3 commented on GitHub (Apr 1, 2023):
@BobWs commented on GitHub (Apr 2, 2023):
reinstall NPM 2.10.2 without PGID/PUID worked for me on Docker Synology DSM 7.1.1!
@Trolann commented on GitHub (Apr 4, 2023):
Tried 2.10.2 and got "No Reason Phrase" and rolling back to 2.9.22 doesn't work anymore. Now my system is down.
Edit:
Error was due to a 'missing' cert (for a host that was removed long ago). I put a dummy cert in its place and the system came up, but would not let me login (same behavior as before). All my routes were also down. 2.10.2 doesn't seem to fix this, and the installation documentation still isn't updated.
Going to give it another few weeks while I'm busy with school and then migrate if it's not sorted.
@drchino commented on GitHub (Apr 5, 2023):
I've rolled back to 2.9.22, still left the PGID/PUID and this worked straight away for me.
Will pause my updates until this is resolved
@IDDQD69 commented on GitHub (Apr 13, 2023):
v2.10.2 seems to be working again at least for me when using host network mode.
@BobWs commented on GitHub (Apr 16, 2023):
v2.10.2 is working for me with macvlan network!
@ituri commented on GitHub (Apr 16, 2023):
Not here. Getting this error:
@fischy667 commented on GitHub (Apr 16, 2023):
To avoid the error
s6-sudoc: fatal: unable to get exit status from server: Operation timed outI added the lineto my docker run command.
With this line and without PUID and PGID it is working fine.
@ituri commented on GitHub (Apr 16, 2023):
Same issue. For reference, here's my docker-compose.yml:
@coalfield commented on GitHub (Apr 20, 2023):
Thanks this fix works for me on latest version with PUID and PGID.
@ljford7 commented on GitHub (May 11, 2023):
Nevermind - fix didn't work.
@jc21 commented on GitHub (May 12, 2023):
v2.10.3 adds an unlimited
S6_CMD_WAIT_FOR_SERVICES_MAXTIMEvalue so it should not timeout anymore.That said, the reason for the startup taking a long time is probably because certbot doesn't cleanup old certs and there will be thousands upon thousands of files in your
letsencryptfolder that are no longer required. The startup tries to change the ownership of that folder.I'd recommend running
cert-prunefrom within the docker container to clean them up.@blaine07 commented on GitHub (May 12, 2023):
Does cert-prune work correctly now mate? At one point it didn’t/needed amended on owners end or something??
@coalfield commented on GitHub (May 12, 2023):
For those still struggling with the I have managed to resolve with the brilliant Marius help. I followed these steps:
Its likely not all those steps are needed and you can bypass the folder rename, but just saying what I did do with it confirmed working.
Note there is no GUID and PUID in the new version of the install. So anyone having issues with this container on synology can follow the above and you should be back up and running. Absolutely no errors on the log.
@rymancl commented on GitHub (May 12, 2023):
With v2.10.3, npm is now working perfectly again on my Synology. 🎉
I removed
from my env vars and that's it.
I tested a fresh install and several server reboots and npm didn't have any issues starting up anymore.
Thanks for the work on this @jc21 !
@boardlord1 commented on GitHub (May 13, 2023):
Can confirm this, updated to 2.10.3 from 2.9.22. At first, it again failed to bind to 0.0.0.0:80 (permission denied), but after commenting out the PUID and PGID env vars for NPM in my Portainer stack and redeploying it, NPM started up no problem. Thanks!
@Turiok commented on GitHub (May 28, 2023):
@maz1987in Hi, If it's corrected. Can you close the issue?
@DDZ-DO commented on GitHub (Jun 27, 2023):
Problem still exists. Tried it with latest release on Ubuntu Server 18.04 LTS.
@BobWs commented on GitHub (Jun 28, 2023):
Problem still exists only when commenting out the PUID and PGID env vars it works!
@newroc commented on GitHub (Jun 28, 2023):
Problem still exists. Tried it with latest release on RouterOS 7.10.1.
I have tried the following scenarios:
@DDZ-DO commented on GitHub (Jun 28, 2023):
Never used PUID or PGID env
@jeph commented on GitHub (Jul 30, 2023):
For people still experiencing this, here's how I got to the latest container without having to do a clean install or anything from version
2.9.22.docker-compose upwith this image:jc21/nginx-proxy-manager:github-uidgiddocker-compose upwith the latest image:jc21/nginx-proxy-manager:latest@pengliaoye commented on GitHub (Aug 7, 2023):
+1. have some issue
@bensmith2697 commented on GitHub (Oct 8, 2023):
Still not working with latest, any update on this?
@urbenlegend commented on GitHub (Feb 13, 2024):
For those suggesting to comment out PUID and PGID, isn't this unwise since NPM will be running as root and if it gets compromised it spells trouble for the rest of the system? I thought it was safer to have PUID and PGID as a regular user. I get the same permission denied on port 80 when I have those variables set though.
If this is intended behavior, is it possible to run NPM on 8080 and 8443 to circumvent this issue? I don't know how exactly to do this. I've already tried specifying
8080:80and8443:443in my docker compose but I still get permission denied.@paoloantinori commented on GitHub (Sep 10, 2024):
For anyone still dealing with this, this works in rootless podman, as of today.
latestdoes not and returns the error in the first post. The solution is to pin the version to2.9.22@johflo commented on GitHub (Sep 16, 2024):
Hi,
I found the possible issue.
I had a container with the bind() to 0.0.0.0:80 failed (13: Permission denied) issue.
After that I made an new npm contaier wich runs without problems. After copying the old proxy and stream configuration teh new container also broke
After deleting the config files, the new container works again. If I make a new configuration, everything works.
@Inareous commented on GitHub (Nov 27, 2024):
For those running rootless podman without host network but want to keep old config, there seems to be a few options:
2.9.22.latest, remove envPUID=1000 and PGID=1000, and do aGIDMap/RemapGidandUIDMap/RemapUidto0:{{your_user}}:1instead.@github-actions[bot] commented on GitHub (Jun 11, 2025):
Issue is now considered stale. If you want to keep it open, please comment 👍
@JBlond commented on GitHub (Jun 17, 2025):
This is not stale
@heinrich-platau commented on GitHub (Jun 19, 2025):
I have installed Nginx Proxy Manager today (19.06.2025) - Version v2.12.3
Had the same problem:
nginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)].
I'm glad to found this post. Did a downgrade to v2.9.22 and it works without any issues.
Is there a newer Version, that already fixed this problem?
@boehle commented on GitHub (Nov 22, 2025):
Ran into the same issue today on TrueNAS Scale. Found this thread, then read the docs: https://nginxproxymanager.com/advanced-config/#running-processes-as-a-user-group where it says:
So just removed the PUID and PGID values from the env section of my compose file and also added the NET_BIND_SERVICE capability, so the container can bind to ports below 1024 without being privileged. And started fine with no issues.
@Modged commented on GitHub (Jan 26, 2026):
I’m running NPM on a Synology NAS using a macvlan network. Despite trying multiple configurations such as mapping high ports (>1024), adjusting environment variables for HTTP, HTTPS, and Admin ports, and using NET_BIND_SERVICE every attempt results in the same error:
I would like to use a limited user instead of the default root.
PUID and PGID other than 0.
And I am facing issue which doesnt occur if I stay with root.
bind() to 0.0.0.0:80 failed (13: Permission denied)
nginx: configuration file /usr/local/nginx/conf/nginx.conf test failed
Initially, I hoped to test changing the internal ports to >1024 to see if that would work before bothering you.
From my research and testing, it appears that the root cause is that macvlan prevents non-root users from binding to privileged ports (<1024) on Synology, and Synology’s kernel does not support ip_unprivileged_port_start.
Internal ports change are ignored.
I tried many times always the same result.
From the doc :
# These ports are in format :
- '80:80' # Public HTTP Port
- '443:443' # Public HTTPS Port
- '81:81' # Admin Web Port
I’m not as skilled in Docker as you are, and I wouldn’t know how to create a Docker project like yours. However, to demonstrate the issue, I created a minimal Docker container using a custom nginx.conf file and configured it to run with a different internal port (8181).
Here’s a brief outline of what I did:
Dockerfile Creation: I created a Dockerfile that uses the official Nginx image and copies a custom configuration file into the container.
Nginx Configuration: The nginx.conf is set to listen on port 8181 instead of the default port 81.
Testing: I ran the container using the macvlan network configuration and was able to successfully access the web interface at http://192.168.0.126:8181, confirming that the setup works without the permission error.
Here is my docker run
Through this setup, it is clear that if I could change the internal port configuration in your Docker setup, the issue would be resolved.
BTW.
Just tried NPMPlus and the issue is gone cause changing internal port is supported :
environment:
- "NPM_PORT=8282"
- "HTTP_PORT=8080"
- "HTTPS_PORT=8443"