mirror of
https://github.com/NginxProxyManager/nginx-proxy-manager.git
synced 2026-04-25 17:35:52 +03:00
[GH-ISSUE #2108] Certificate Assocation lost after ACL is edited #1519
Labels
No labels
awaiting feedback
bug
cannot reproduce
dns provider request
duplicate
enhancement
enhancement
enhancement
good first issue
help wanted
invalid
need more info
no certbot plugin available
product-support
pull-request
question
stale
troll
upstream issue
v2
v2
v2
v3
wontfix
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference
starred/nginx-proxy-manager-NginxProxyManager#1519
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @aaronbolton on GitHub (Jun 13, 2022).
Original GitHub issue: https://github.com/NginxProxyManager/nginx-proxy-manager/issues/2108
When editing an ACL Subnet list associated with a proxy host with an SSL Cert the cert becomes unassigned and reverts back to the localhost cert
@pmoon00 commented on GitHub (Jun 20, 2022):
+1 I am also experiencing this.
@jeanpaulrh commented on GitHub (Jun 20, 2022):
me too, but it seems that to select the certificate again fixes it also for all other hosts (at least to me but I've been trying all sort of stuff thinking I had messed up something so maybe YMMV)
@mvnmgrx commented on GitHub (Jan 8, 2023):
+1 the same problem here. When editing an ACL, all assigned hosts with LetsEncrypt Certificates will loose their SSL configuration.
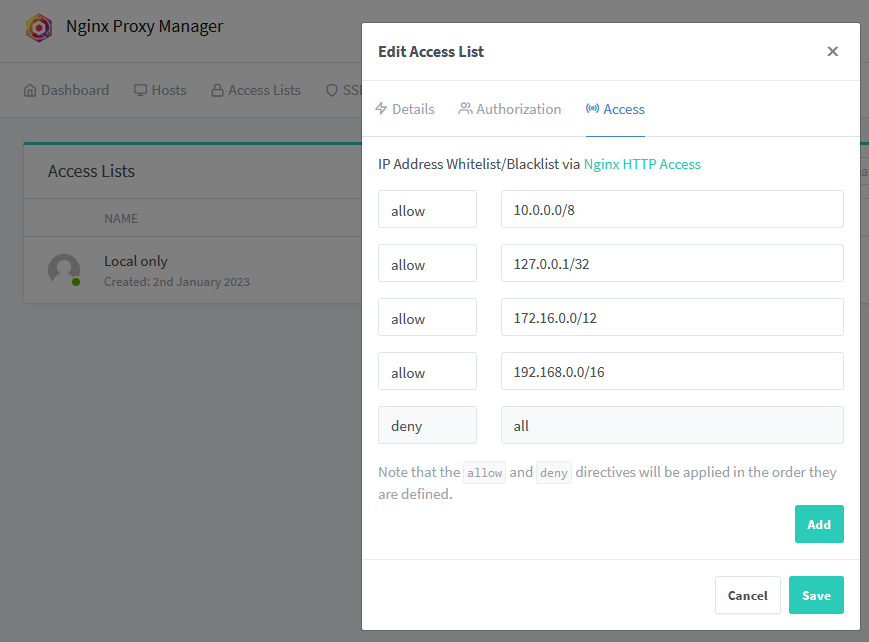
To recreate:
allow xxx.xxx.xxx.xxxand onedeny allentryNPM version: v2.9.19
Deployment: Docker container managed with docker-compose on Debian Bullseye
Docker engine version: 20.10.22
docker-compose version: v2.14.2
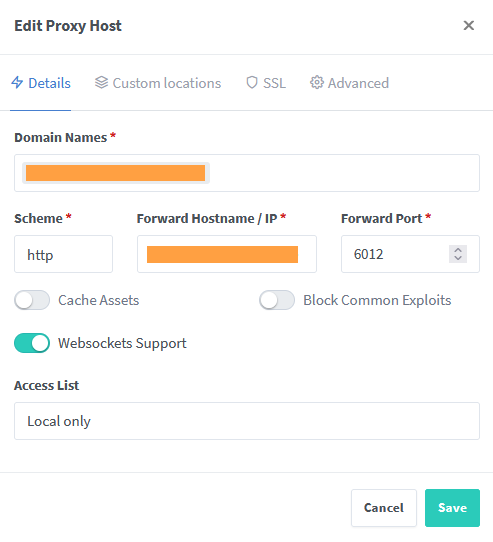
A proxy host configuration before editing the ACL:
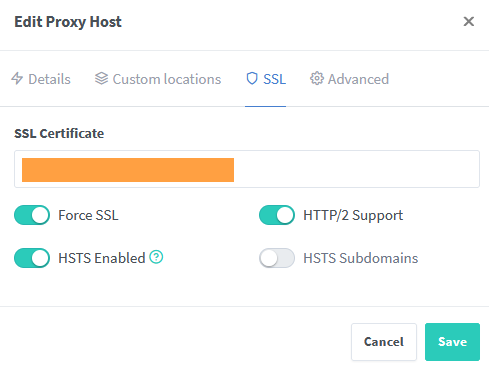
Same config after editing the ACL:
Screenshots: