mirror of
https://github.com/NginxProxyManager/nginx-proxy-manager.git
synced 2026-04-25 01:15:51 +03:00
[GH-ISSUE #141] New Proxy Host + SSL #126
Labels
No labels
awaiting feedback
bug
cannot reproduce
dns provider request
duplicate
enhancement
enhancement
enhancement
good first issue
help wanted
invalid
need more info
no certbot plugin available
product-support
pull-request
question
stale
troll
upstream issue
v2
v2
v2
v3
wontfix
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference
starred/nginx-proxy-manager-NginxProxyManager#126
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @nunofmds on GitHub (May 10, 2019).
Original GitHub issue: https://github.com/NginxProxyManager/nginx-proxy-manager/issues/141
Checklist
jc21/nginx-proxy-manager:latestdocker image?Yes
Yes
Yes
Describe the bug
A clear and concise description of what the bug is.
When add a New Proxy Host with Request New SSL Certificate option there is a Timeout and after refresh the New Proxy Host appears and Certificate as well but it's unusable since there is nothing at the directory of certificates.
As workaround I created the Proxy Host first, went to SSL Main Tab to generate the certificate, went back to Proxy Host and associate it.
What version of Nginx Proxy Manager is reported on the login page?
v2.0.13
To Reproduce
Steps to reproduce the behavior:
Expected behavior
First time I used this manager everything worked like a charm. This start happening after I tried to renew the certificates since they expired...Maybe it's related to the fact that certificates was generated before. I reinstalled the full manager with the cleanup of data directories, downloaded the latest docker image and behavior was the same even if I used the new renew option.
Screenshots
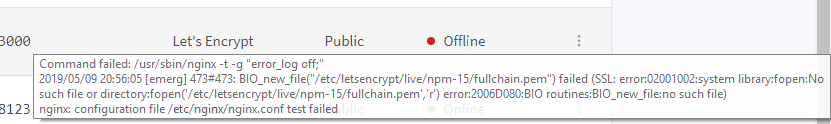

If applicable, add screenshots to help explain your problem.
Operating System
Additional context
Add any other context about the problem here, docker version, browser version if applicable to the problem. Too much info is better than too little.
Errors
Command failed: /usr/bin/certbot renew -n --force-renewal --disable-hook-validation --cert-name "npm-2" ,
Saving debug log to /var/log/letsencrypt/letsencrypt.log,
No certificate found with name npm-2 (expected /etc/letsencrypt/renewal/npm-2.conf).,
@OhHeyAlan commented on GitHub (May 10, 2019):
@xNuno This is not a bug, you can't request TLS certs for your localhost
192.168.1.10from a CA. CA's will only issue certs for a TLDexample.comyou have control of.You can try creating a self-signed cert to be used on your localhost but you'll get insecure browser warnings.
@nunofmds commented on GitHub (May 10, 2019):
@OhHeyAlan, I didn't request certificate for my localhost...I just used my lan ip to reach Proxy Manager... I request it for a duckdns domain... Of course it works for my domain because if I do 1 step at time like I explained it works...
@OhHeyAlan commented on GitHub (May 10, 2019):
@xNuno Have you checked the folder for
/etc/letsencrypt/renewal/npm-2.confto see if it exist?Try removing the certs from
letsencrypt/live/npm-and just creating new ones. That'll get you back up and running.@nunofmds commented on GitHub (May 10, 2019):
@OhHeyAlan, tried that before... Did you try to reproduce the steps I refer? Maybe it's only me with this...
@OhHeyAlan commented on GitHub (May 11, 2019):
I personally use a wildcard cert from certbot. I've set it up via a volume in docker-compose so its automatically applied to all domains by default...
@jc21 commented on GitHub (May 12, 2019):
Whenever you see "Internal Error" in the UI, then some shit is broken.. What does the
docker logssay for that error?In the latest release I increased the XHR timeout to 30 seconds so requesting a LE cert shouldn't cause problems, but it looks like you're renewing and for some reason, the certificate you're renewing isn't fully configured on disk anymore.
Everything is working fine on my production with the latest version. If you don't have much to setup, it might be worth starting fresh?
@nunofmds commented on GitHub (May 13, 2019):
@jc21, yep...I installed everything from scratch and it's ok if I do first the proxy add and after the certificate request. Maybe is the timeout don't know. I remember to see something on the logs point to .wellknow url but that was not available when I tried manually.
This can be caused on the time you make a new certificate there is a validation from let's encrypt to make sure you are the owner of the dns...
If you can't reproduce let's close this till I found more info.
@battilo commented on GitHub (Jun 25, 2019):
Hi everyone... I have the same problem in a new installation into a freenas vm.
I also use the duckdns ddns service.
I didn't found the "Let's Encrypt" certs in right path... every time I tried, I had the same result.
This evening I'll try to create the certs before.
@nunofmds commented on GitHub (Jun 25, 2019):
Hi,
Make sure you are forwarding port 443 and 80 to your server...
Regards,
Nuno Silva
@Sigri44 commented on GitHub (Jul 23, 2019):
Good morning, everyone!
I managed to fix this "internal error" problem. In fact, it only comes into play if you activate SSL on your host, and especially if you activate SSL when you have not yet created your domain (or it is not yet deployed... ! ; ;)).
I did different tests, creating the domain, then enabling the host (without SSL!) in NPM it works. if you enable SSL by returning to the settings, internal error, but once the domain is created, then no SSL error, even creating everything in one step :)
@jc21 commented on GitHub (Jul 23, 2019):
Duplicate of #133
@axute commented on GitHub (Sep 17, 2020):
i dont think it is a duplicate of #133 .
i use raspberry3 and odroid (hc1) and have also a timeout (odroid runs with ssd-hd and 8 cores).
In the container logs i can see the letsencrypt request, it took 37 seconds (minimum). The ajax request will canceled after 30 seconds.
github.com/jc21/nginx-proxy-manager@28f72086ec/frontend/js/app/api.js (L56)I also believe that the certificate request takes longer with each certificate in my store - but that's just a subjective perception.
@chaptergy commented on GitHub (May 10, 2021):
A lot has changed since this issue was opened and since the last comment was made. If this is still a problem, please open a new issue. Maybe even a feature request, like configurable letsencrypt timeouts. Though this is basically possible using a DNS challenge.
@axute commented on GitHub (May 12, 2021):
switched to traefik2, sorry - no ui, but works.