mirror of
https://github.com/NginxProxyManager/nginx-proxy-manager.git
synced 2026-04-25 09:25:55 +03:00
[GH-ISSUE #1510] Block Incomming for Dockernetworks #1157
Labels
No labels
awaiting feedback
bug
cannot reproduce
dns provider request
duplicate
enhancement
enhancement
enhancement
good first issue
help wanted
invalid
need more info
no certbot plugin available
product-support
pull-request
question
stale
troll
upstream issue
v2
v2
v2
v3
wontfix
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference
starred/nginx-proxy-manager-NginxProxyManager#1157
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @calvinthefreak on GitHub (Oct 21, 2021).
Original GitHub issue: https://github.com/NginxProxyManager/nginx-proxy-manager/issues/1510
Is your feature request related to a problem? Please describe.
I am not that Happy with the "Docker-Attach" Network feature.
Since I am running potentially wnsafe apps behind the Proxymanager inside the docker-networks, I want to Isolate the WebUI.
So, when I am attaching the "app" container to an network, to let it see the Backend, I don't want the backend to be able, to access all Ports on the "app" container.
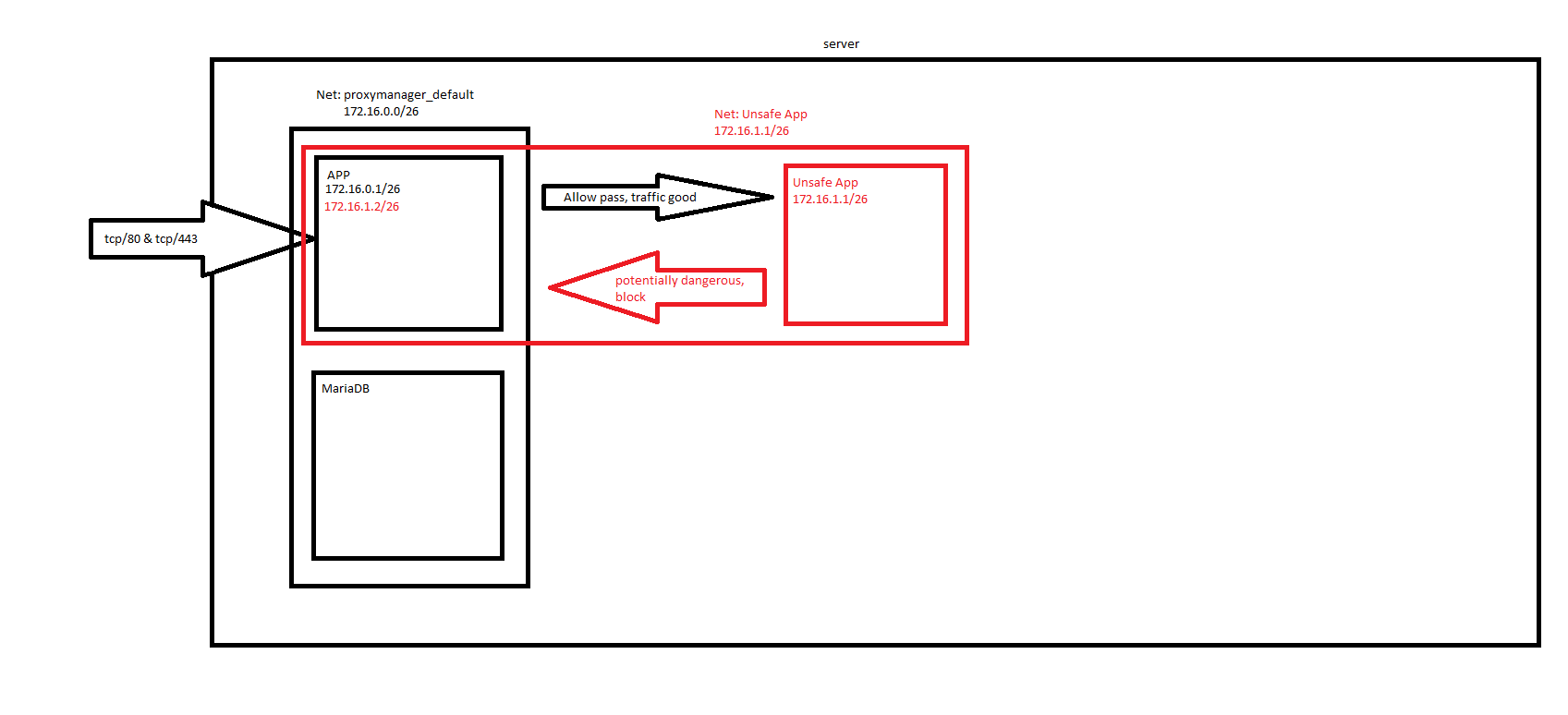
Schematic:
Describe the solution you'd like
Propably the functionality, to blacklist the IPs from accessing incomming to the Container.
I googled for iptables functionality, I found the following:
https://dev.to/andre/docker-restricting-in--and-outbound-network-traffic-67p
You could propably implement blacklisting on IP-Adress base like this example shows (changed a bit, to block and allow the rest):
and running this with the Enrtypoint to be filled with an ENV, so that it is only applied when the User sets this variable.
Describe alternatives you've considered
Building a proxy for the Proxy... or lets say, a firewall container... but I am quite unsure how to do this.
Additional context
@calvinthefreak commented on GitHub (Oct 21, 2021):
It would also be possible, to ship the container with UFW and iptables and make it persistant.
@calvinthefreak commented on GitHub (Oct 21, 2021):
Well, who cares, I build my self a new overlay:
Create following files in the same dir:
"iptables-service":
"iptables.rules":
and finally a "Dockerfile":
After that, you can build a new Overlay:
docker build -t 64i.de/nginxproxymanager .64i.de/nginxproxymanager is the new Packagename.
So in your dockercompose on the block "app" place '64i.de/nginxproxymanager' as image.
Best Regards. Calvin.
@github-actions[bot] commented on GitHub (Mar 2, 2024):
Issue is now considered stale. If you want to keep it open, please comment 👍
@github-actions[bot] commented on GitHub (Apr 15, 2025):
Issue was closed due to inactivity.