mirror of
https://github.com/lldap/lldap.git
synced 2026-04-25 16:25:55 +03:00
[GH-ISSUE #247] Support for reverse proxies #86
Labels
No labels
backend
blocked
bug
cleanup
dependencies
docker
documentation
duplicate
enhancement
enhancement
frontend
github_actions
good first issue
help wanted
help wanted
integration
invalid
ldap
pull-request
question
rust
rust
tests
wontfix
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference
starred/lldap-lldap#86
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @k3nd0x on GitHub (Jul 13, 2022).
Original GitHub issue: https://github.com/lldap/lldap/issues/247
Hi,
I really appreciate your work :)
can you please add the option to change the subdirectory of the webinterface. It is much easier to reverse proxy a request to for example /lldap than to /
State now: http://0.0.0.0:17170/
Example cool for reverse proxies: http://0.0.0.0:17170/lldap/
@nitnelave commented on GitHub (Jul 13, 2022):
I'm not sure I understand why it makes it easier:
In both cases, you don't really need help from LLDAP. What reverse proxy are you using? Maybe someone can help you with the precise config needed.
@k3nd0x commented on GitHub (Jul 15, 2022):
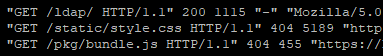
I'm using apache as reverse proxy. The "problem" are the subdirectories. LLDAP provides the static/ and the pkg/ folder directly to https://example.com/static but they are at https://example.com/ldap/static.
The apache config is complex as hell:
<Location /ldap/>
ProxyPass http://:17170/
ProxyPassReverse http://:17170/
Of course i can add some rules to the apache config to catch the real directories but it is easier for everybody with a subdirector that is directly provided by the LLDAP Container :)
With a own subdomain it is no problem, but I don't want to create a own subdomain for every software :)
In the most selfhosted software solution you can change this setting (for example: grafana, icinga, promtheus, SOGo, vaulwarden...)
@nitnelave commented on GitHub (Jul 15, 2022):
I'll see if I have time for this later on, but given that it can be easily addressed with reverse proxy configuration (you just need to handle the
staticfolder and*.html/jsfiles), it's not very high on my list.@Roemer commented on GitHub (Oct 13, 2022):
I think getting the reverse proxy to work correctly is not that easy without a possibility to tell lldap a base-path. In fact, I do not know a working nginx configuration. So I think this should be a bit higher on the list ;)
@nitnelave commented on GitHub (Oct 14, 2022):
I'm always open to PRs!
@wailashi commented on GitHub (Oct 25, 2022):
FWIW I'm running lldap behind Traefik and https://lldap.example.com/ works fine with no modifications to lldap or base-path shenanigans.
@Cyrix126 commented on GitHub (Nov 8, 2022):
nginx configuration which works for me for https://ldap.example.com
@khangp0000 commented on GitHub (Feb 14, 2023):
So I look into this a bit (because I want path reverse proxy rather than host reverse proxy). These changes would be required:
/subpath) into run command [EASY] (Server)::scopeto all endpoint [EASY] (Server)basetag into index html, something like:<base href="/subpath" />and fix all
fetch(or rather yew'sRequest) call to accept the base url. We can pass around thebasenamefield which was initialized by yew inRouter,Link, e.t.c. objects [HARD] (UI)index.htmlsomehow, maybe using a string template engine, or just load the whole html into memory and prepend the tag. [EASY-MEDIUM]Also we should rename this issue to something like
Add basepath supportorPath based reverse proxy supportbecause domain based reverse proxy is still working as mentioned above.@nitnelave commented on GitHub (Feb 16, 2023):
I didn't investigate this properly, but if what you say is true, then the biggest blocker I see is updating yew/yew_router. This requires a huge change in how the frontend is written (not conceptually, thankfully, but the syntax is very different). I'll open an issue for that.
@infogulch commented on GitHub (Feb 25, 2023):
Not to rain on anyone's parade, but I haven't seen this stated yet... There is a cross-contamination security risk from hosting multiple applications in different paths on a single domain, which is particularly impactful in this case because lldap acts as the root of trust. I think it would be reasonable for an "opinionated, simplified LDAP" server to have the opinion that it should be hosted on its own dedicated domain.
@nitnelave commented on GitHub (Feb 25, 2023):
@infogulch could you expand on the security risk? Or do you have documents/articles that I could read about it? I'm curious
@infogulch commented on GitHub (Feb 26, 2023):
Sure, this comes down to basic browser security protocols like the Same-origin policy and CORS.
An example attack would be an application in a different directory is exploited (e.g. fails to sanitize a
<script>element out of a user comment) making a request to an endpoint in the lldap app, and the browser happily makes the request using the lldap app's cookies. Technically speaking, if everything is set up correctly (cookies, headers, etc), I believe it's possible to make this design secure. But at best I would describe this as precarious.Here are some stackexchange discussions about it:
Preventing insecure webapp on subdomain compromise security of main webapp
(This has links to a bunch of related discussions.)
Is security increased by using a subdomain per customer in a web-app?
Some web app management platforms have a policy to run every app on its own subdomain, which offers a good balance of admin cost and security. For example, Cloudron, which I use.
@Fawa commented on GitHub (Mar 30, 2023):
You able to post your Traefik labels for this? This is the only container I can't seem to get to work with Traefik, just get a gateway timeout after about 30 seconds. Below is what I run for my other 30ish containers without issue, couldn't seem to get lldap to agree with it, even after adjusting the TOML file with the relevant info. (or is that where my issue lies?). Just know I am knew to LDAP stuff.
@nitnelave commented on GitHub (Mar 30, 2023):
Just a note on a potential TCP router for the LDAP ports. The TCP router is only needed if you want to expose the LDAP traffic to internet. This is highly not recommended since LDAP is not encrypted and the passwords are in plain text. You would at least want to use LDAPS (with an SSL layer), but the best is probably to restrict LDAP traffic to your local host, or even inside the docker networks.
Now, back to @Fawa's question:
EDIT: Reworded the first sentence since the proposal for a TCP router was deleted.
@wailashi commented on GitHub (Mar 30, 2023):
Good point. I should have mentioned the security aspects. I've deleted my comment to avoid leading people astray.
@nitnelave commented on GitHub (Aug 3, 2023):
I'm going to close this as not completed, in parts due to lack of time, and in part due to the security concerns.
@habr05 commented on GitHub (Mar 24, 2024):
"The least robust strategy is to serve all of your customers from your same domain (e.g., mysite.com/customera, mysite.com/customerb; or mysite.com with a different login per customer). The downside of this approach is that you can no longer rely upon the browser's same-origin policy to help you keep customers separate, so now the responsibility passes to your server."
This concern is out place, I think. LDAP is not a random end-user nor intended to be exposed to the web system. There are more robust, dedicated players that handle web facing IAM.
As for sub-folder and sub-domain, that choice should be left to intended audience. Everyone has different requirements, environment and constrains.
@nitnelave commented on GitHub (Apr 3, 2024):
@habr05 it's possible (but not officially supported) to use a reverse-proxy to serve LLDAP on a subpath, see https://github.com/lldap/lldap/issues/870#issuecomment-2004237991
@Zepmann commented on GitHub (Dec 5, 2024):
An unsupported method using nginx to rewrite HTTP headers and content is noted here: https://github.com/lldap/lldap/issues/1055#issue-2720098045
@rhclayto commented on GitHub (Apr 9, 2025):
Please add this feature if time permits, & leave the security cost:benefit analysis to the system administrators. Whether there is any security problem in practice, not just in theory, is highly dependent on context.
@nitnelave commented on GitHub (Apr 9, 2025):
It's already somewhat ready to do: https://github.com/lldap/lldap/issues/870
I'd rather make the insecure things hard to do but not impossible than just documenting them (because people who have security holes don't read the docs), so I think the status quo is reasonable.
@Zepmann commented on GitHub (Apr 9, 2025):
That does not make any sense. If people who have security holes do not read documentation then it does not matter what you write in the documentation. Just ensure that the default configuration is secure.
I am wary of security products that rely on security by obscurity. Do not go down that path, please.
@nitnelave commented on GitHub (Apr 9, 2025):
This is hardly security through obscurity, there is no security hole that I hope no one notices. This is making the insecure things hard. What you're asking for, secure defaults, is exactly what I'm doing: the default thing is secure (one domain for LLDAP), and the insecure thing (shared domain) is possible but harder (and not officially documented apart from issues).
@Zepmann commented on GitHub (Apr 10, 2025):
Not documenting an insecure function due to it being insecure is security through obscurity. "It is secure as long as someone does not know about..." is the definition of security through obscurity, after all.
My preference for these kind of things is documenting them with a big fat warning at the top and call it a day. You are not responsible for how others use LLDAP. It is up to system administrators to make the security risk/functional reward-analysis themselves based on provided information.
@nitnelave commented on GitHub (Apr 10, 2025):
In this case I disagree. It's not "don't enable that option because it's unsafe", but "don't modify the provided software in unsupported ways to do something unsafe because that's, uhh, unsafe". The software, as provided, doesn't support sub-paths. You can overwrite a provided file with a custom one to enable that, but at that point that's your problem, you can't really come back here and say that LLDAP is unsafe.
As for "let admins be admins", this software is opinionated, and one of the core tenets is that it should be easy/safe to use by inexperienced sysadmins. I am trying very hard to reduce any sharp edges, I do not need or want big fat red warnings.
@Zepmann commented on GitHub (Apr 10, 2025):
You state doing this is unsafe as an absolute fact, while it does not have to be. It could be unsafe if a sysadmin is not aware of the risks and just does it based on some comments in some obscure discussion.
I think this is how inexperienced sysadmins stay inexperienced. It can also be documented as unsupported ("here be dragons") and only have the big fat red warning in the documentation where it is warranted. That is how inexperienced sysadmins become experienced, because they can learn what they can do but probably should not do. This knowledge will also help them in being a good sysadmin with different products.
Of course I will respect your vision for LLDAP. It's great and I use it every day! Just be ready to have this question asked more often due to LLDAP becoming more popular. 😄
If you are open for a PR I might see if I have some time in the future to document this with proper warnings to have a good reference for when this discussion pops up again ("this is community documentation, unsupported, unsafe, and you really should not do this because...)". If you are not, all's well. 👍
[edit]
I can also host this documentation somewhere else if you'd like, so it has no official link to LLDAP (community contribution). It can be useful to refer to in a discussion. Just let me know what you think is most convenient. I am also willing to give it a rest. For my use case I have solved this issue, so I am fine either way.
@nitnelave commented on GitHub (Apr 10, 2025):
With respect to educating admins, let them break their teeth on a project with a better support structure :D I don't have time for this, part of the opinionated structure of LLDAP is to reduce the maintenance burden.
As for appetite for PRs, I'd rather stay with the status quo for now until I'm fed up with the requests