mirror of
https://github.com/lldap/lldap.git
synced 2026-04-25 08:15:52 +03:00
[GH-ISSUE #330] Allow browsing with tools like LDAP Admin #125
Labels
No labels
backend
blocked
bug
cleanup
dependencies
docker
documentation
duplicate
enhancement
enhancement
frontend
github_actions
good first issue
help wanted
help wanted
integration
invalid
ldap
pull-request
question
rust
rust
tests
wontfix
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference
starred/lldap-lldap#125
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @Roemer on GitHub (Oct 13, 2022).
Original GitHub issue: https://github.com/lldap/lldap/issues/330
Sometimes it is easier to browse the LDAP tree with tools like LDAP Admin (https://sourceforge.net/projects/ldapadmin/files/ldapadmin/). Right now it fails doing so but maybe it is an easy fix to get that working. I remember GLAuth had the same problem initially but that somehow got fixed and it is now browsable with those tools.
@nitnelave commented on GitHub (Oct 13, 2022):
Can you run LLDAP with
--verboseand paste the logs after trying to see stuff with ldapadmin? (only until you get the first error/missing info in ldapadmin, I don't need pages and pages of logs).@Roemer commented on GitHub (Oct 13, 2022):
When connecting with LDAP Admin, you need to fetch the DNs (dc=example,dc=com). When trying that, I do not get them back and get the following debug messages:
@Roemer commented on GitHub (Oct 13, 2022):
If i manually enter the DN and try to get the data, I get
Could not parse base DN: ""in LDAP Admin and the following log in LLDAP:@nitnelave commented on GitHub (Oct 13, 2022):
Yeah, I see, it's querying a few global properties that are not implemented. It should be rather easy to implement, but it's not very high on my priority list. The web UI is supposed to be the simpler way to access the data.
@nitnelave commented on GitHub (Oct 19, 2022):
Once #345 is pushed, can you check if that solves your issues? If the tool relies on querying the schema, though, that's going to be much harder to fix (and I'm not sure I want to).
@Roemer commented on GitHub (Oct 19, 2022):
Awesome yes, it is now browsable which already helps a lot. Only issue is that the
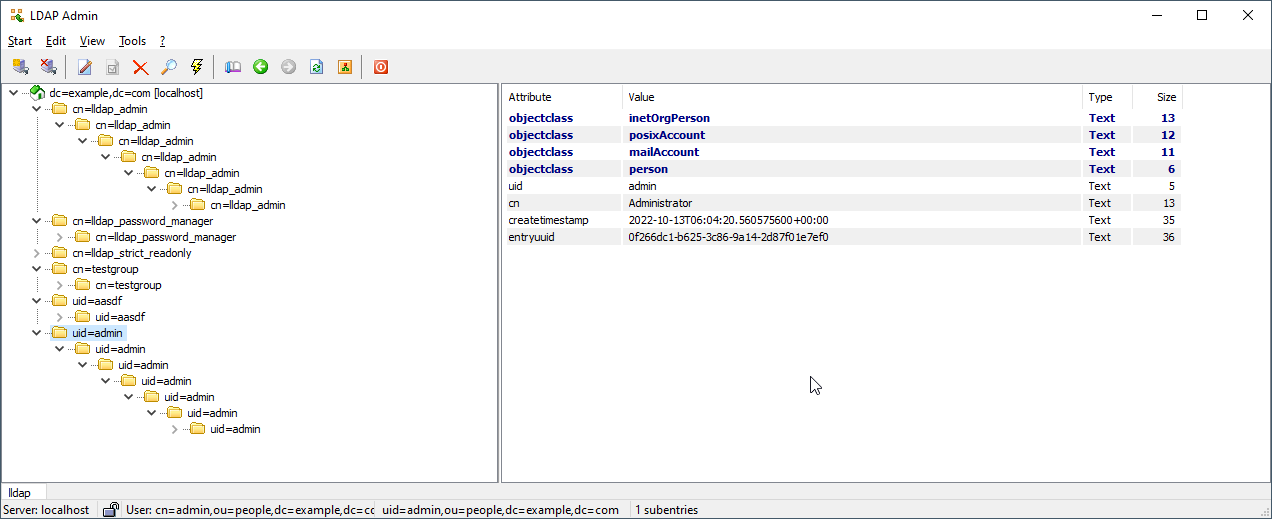
ous are not visible and all entries basically are an endless tree always containing themselves :) See the screenshot:@Roemer commented on GitHub (Oct 19, 2022):
Also it seems that quite some attributes are now shown or missing:
memberoffor the user (maybe that's the issue why this does not work in Jenkins as well?)objectclassofgroupOfUniqueNames@nitnelave commented on GitHub (Oct 20, 2022):
To be fair, I don't care that much how it renders in the LDAP viewer. I'd have to add special code to handle the OUs, debug why it thinks there's nesting, why memberOf is not returned and so on, but that's not really a priority.
I fixed the rootDse response (the metadata about the whole server) because it was easy, but the rest I'm not that interested. I would maybe accept PRs if they don't complicate the code too much.
But to be honest: what's the point? You have a web frontend that's the golden standard, and you even have a semi functional readonly LDAP viewer. Why do you need more than that?
@Roemer commented on GitHub (Oct 20, 2022):
The Web-UI shows a very abstracted form of all the data. To configure LDAP for a service, it is the easiest to just see the "raw" data of the objects (which attributes are available, which values are they set to, which objectclasses exist, ...). But I am totally fine with the current stage. Once I have my vscode-dev-container running I can give it a go to improve that further.
@nitnelave commented on GitHub (Oct 20, 2022):
I agree that some improvements are needed for the front-end: I want to put (at least for the admin) more LDAP information there. There's some work that'll wait until #67 is done, since it'll expose some of the LDAP schema for configuration and display.
@nitnelave commented on GitHub (Oct 20, 2022):
I'm closing this issue for now since the very basic functionality is there, we can open more specific issues later on if needed.