mirror of
https://github.com/hickory-dns/hickory-dns.git
synced 2026-04-25 11:15:54 +03:00
[GH-ISSUE #1819] cloudflare_tls failed, both dns-over-native-tls and dns-over-rustls tls handshake stuck #780
Labels
No labels
blocked
breaking-change
bug
bug:critical
bug:tests
cleanup
compliance
compliance
compliance
crate:all
crate:client
crate:native-tls
crate:proto
crate:recursor
crate:resolver
crate:resolver
crate:rustls
crate:server
crate:util
dependencies
docs
duplicate
easy
easy
enhance
enhance
enhance
feature:dns-over-https
feature:dns-over-quic
feature:dns-over-tls
feature:dnsssec
feature:global_lb
feature:mdns
feature:tsig
features:edns
has workaround
ops
perf
platform:WASM
platform:android
platform:fuchsia
platform:linux
platform:macos
platform:windows
pull-request
question
test
tools
tools
trust
unclear
wontfix
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference
starred/hickory-dns#780
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @mokeyish on GitHub (Nov 2, 2022).
Original GitHub issue: https://github.com/hickory-dns/hickory-dns/issues/1819
Describe the bug
cloudflare_tls failed, both dns-over-native-tls and dns-over-rustls tls handshake stuck.
cloudflare_tlsfailed whilecloudflare_httpsis success.It seems internal ignore the ip address defined in NameServerConfig, and query ip address withcloudflare-dns.comagain.To Reproduce
Steps to reproduce the behavior:
DOT
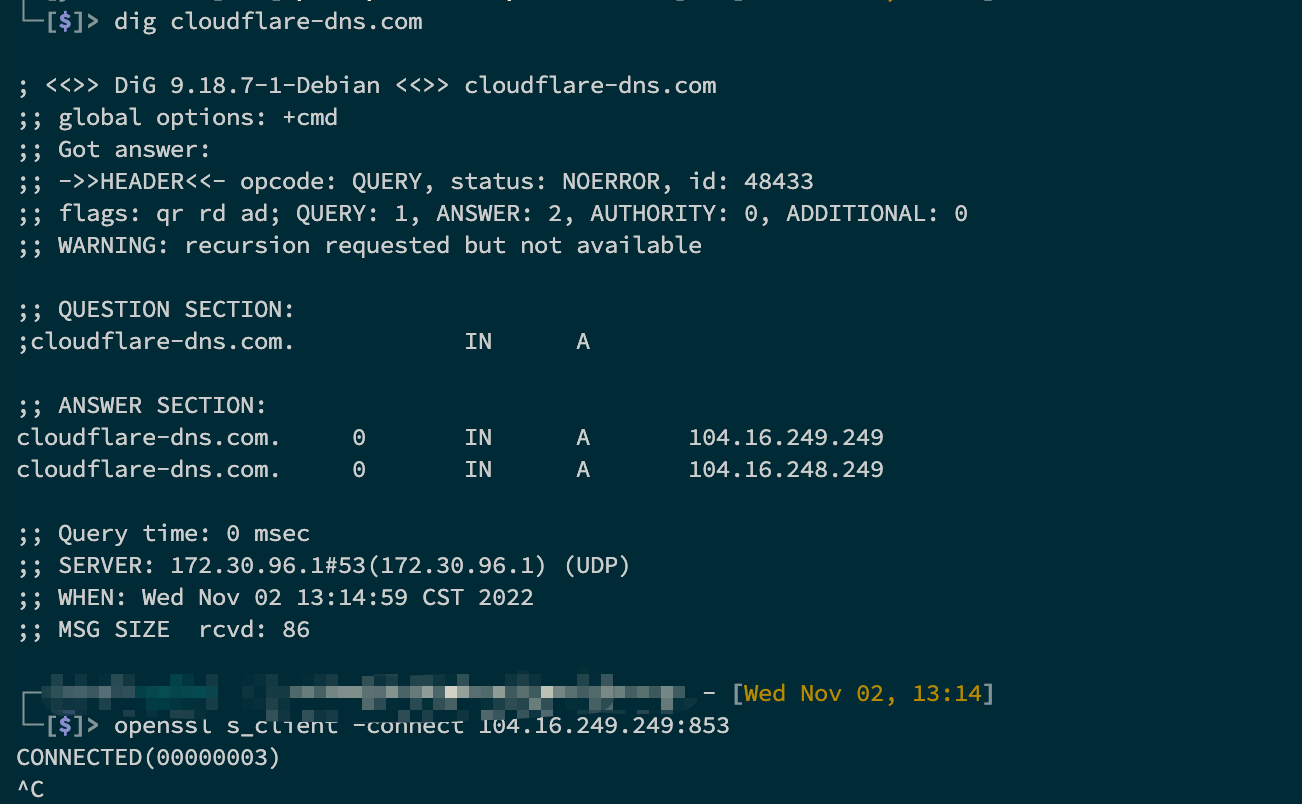
DOH
Expected behavior
Success to query the dns records.
System:
Version:
Crate: resolver
Version: 0.22.
Additional context
BTW: If I set a breakpoint on
resolver.lookup_ip(name).await, then debug, It will query the records successfully.The reproduce code:
The output when set a breakpoint then debug:
The output run directly:
@mokeyish commented on GitHub (Nov 2, 2022):
This line stuck
github.com/bluejekyll/trust-dns@fe70e51f5d/crates/resolver/src/name_server/connection_provider.rs (L326)and throw
Is there any way to fix it? set a breakpoint on the line, it can retry, and get the final dns records.
@mokeyish commented on GitHub (Nov 2, 2022):
I solve this probelm temporarily by adding a
DelayFutureand sleep 800 millis.@djc commented on GitHub (Nov 2, 2022):
I tried running your reproduction code but it returns immediately with a lookup result for me. Please give me better instructions on how to reproduce this issue.
@mokeyish commented on GitHub (Nov 2, 2022):
@djc Thanks, maybe we are in different network environment,if i use google_tls, it also retuns immediately,it seems check server response too quick in tls handshaking. after I add delay 800ms,it will return lookup results, if the delay lower 800ms may fails.
@mokeyish commented on GitHub (Nov 3, 2022):
@djc Hello,
I add some logging to MidHandshake, Do you have any ideas to solve this problem? It seems never poll MidHandshake second time if I don't add a delay Future.
The Failed screenshot.
The Success screenshot, Wrap the FirstAnswerFuture with a new DelayFuture and sleep 1 second before polling FirstAnswerFuture.
The code of DelayFuture
@mokeyish commented on GitHub (Nov 4, 2022):
The trust-dns internal tests also stuck, while i query with
dogsuccess.The dog tool : https://github.com/ogham/dog
@mokeyish commented on GitHub (Nov 4, 2022):
@djc Hello,
Do you have IPv6 address? I can provide a docker environment to reproduce it, but the docker container only has IPv6 address.
I found that both
native-tlsandrustlswill get stuck in , maybe a bug with https://github.com/tokio-rs/tls in weak network environment.@djc commented on GitHub (Nov 4, 2022):
I'm also a tokio-rustls maintainer, if you can isolate the bug to that level probably makes sense to file an issue there.
@mokeyish commented on GitHub (Nov 4, 2022):
The docker environment did't modify anything, just run the unittest here to reproduce,
github.com/bluejekyll/trust-dns@ccd875bce4/crates/resolver/src/tls/mod.rs (L72)@rohitcoder commented on GitHub (Jan 18, 2023):
Hi Guys, Just wanted to check if anyone found solution for this, actually i'm using
reqwestcrate in rust and i'm trying to usedanger_accept_invalid_certs(true)to avoid this TLS issue for Cloudflare, anyone found solution?@mokeyish commented on GitHub (Jan 18, 2023):
@rohitcoder I ended up solving it by disabling sending SNI names. Because the ISP shields it by detecting the plaintext SNI in the first few bytes of TCP.
Here is my code:
github.com/mokeyish/smartdns-rs@785a66c387/src/dns_client.rs (L551)This issue should be closed.