mirror of
https://github.com/brentvollebregt/auto-py-to-exe.git
synced 2026-04-25 19:55:49 +03:00
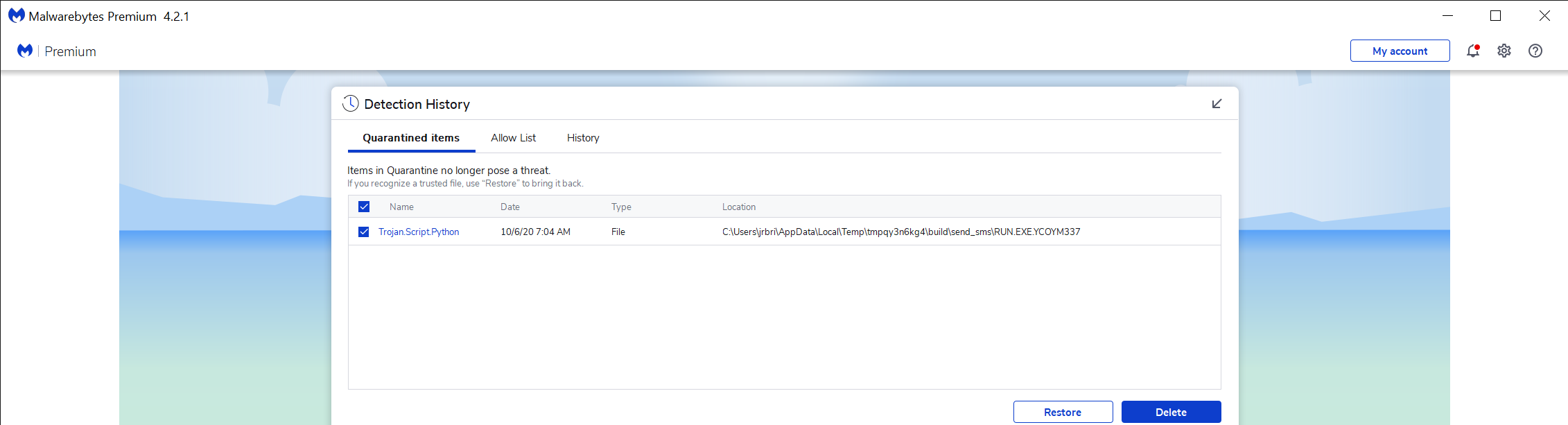
[GH-ISSUE #125] MalwareBytes detects Trojan.Script.Python on a temp file after compiling a script #119
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @jb2kewl on GitHub (Oct 6, 2020).
Original GitHub issue: https://github.com/brentvollebregt/auto-py-to-exe/issues/125
I compiled a fairly simple aws script to send a sms message.. Later malware bytes picked up a temp file from this auto-py-to-exe and said it had a trojan in it.
after compiling the below script, a full machine scan picked up this file as having a trojan in it... (secrets.py just has the secret variables for this script)
(.venv) PS C:\Dev_Python\aws\sendsms> python --version
Python 3.8.5
Temp file detected with Trojan: c:\users\jrbri\AppData\Local\Temp\tmpqy3n6kg4\build\send_sms\RUN.EXE.YCOYM337
File send_sms.py:
import boto3
import secret
import sys
import re
import argparse
import os.path
from os import path
sDescText = """
Sends a sms message to a specific phone number:
Example usage:
send_sms.exe +17195551212 "Your Message"
"""
this is a pointer to the module object instance itself.
this = sys.modules[name]
parser = argparse.ArgumentParser(sDescText)
parser.add_argument("number", help="Enter the phone number here. Example: +17195551212")
parser.add_argument("message", help='Enter your SMS message in double quotes. Example: "Hello World"')
args = parser.parse_args()
if args.number != secret.aws_example_number:
sys.exit("Invalid Phone Number!")
print(args.number,":", args.message)
Create a SNS client
client = boto3.client(
"sns",
aws_access_key_id=secret.aws_key_id,
aws_secret_access_key=secret.aws_key_val,
region_name=secret.aws_region
)
Send your sms message.
client.publish(
PhoneNumber=args.number,
Message=args.message
)
requirements.txt
send_sms - Copy.txt
@brentvollebregt commented on GitHub (Oct 7, 2020):
Have you read brentvollebregt/auto-py-to-exe#122?
@brentvollebregt commented on GitHub (Jan 19, 2021):
Closing due to no activity in more than three months and no more information provided about the issue.