mirror of
https://github.com/opensolutions/ViMbAdmin.git
synced 2026-04-26 08:45:54 +03:00
[GH-ISSUE #253] Cross Site Scripting at /auth/lost-password #202
Labels
No labels
bug
feature
feature
improvement
improvement
pull-request
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference
starred/ViMbAdmin-opensolutions#202
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @kendyhikaru on GitHub (Sep 20, 2018).
Original GitHub issue: https://github.com/opensolutions/ViMbAdmin/issues/253
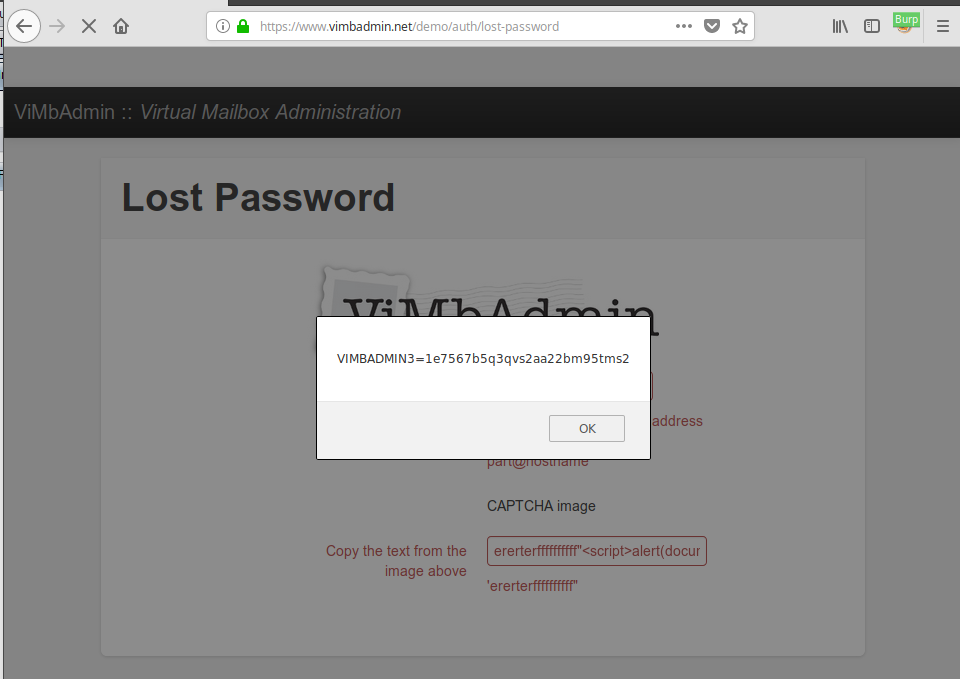
Lost Password had vulnerability, if parameter captchatext longer than 10 characters, application with print out. Attacker can inject javascript in to captchatext parameter with more than 10 characters to exploit Cross Site Scripting. This is POST message:
After submit, javascript will run on browser: