mirror of
https://github.com/brutaldev/StrongNameSigner.git
synced 2026-04-25 11:26:04 +03:00
[GH-ISSUE #61] SNS is modifying assemblies in the NuGet package cache #52
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @robertmclaws on GitHub (Mar 27, 2021).
Original GitHub issue: https://github.com/brutaldev/StrongNameSigner/issues/61
Originally assigned to: @brutaldev on GitHub.
I'm trying to compile the RESTier project using this library, and since the project binaries are signed, and their internals are exposed to the unit test projects, I also need to strong name the unit tests. One of the libraries it uses (Simple.OData.Client) is not signed, so we're using this NuGet package to sign it.
That client references NuGet package dependencies that are already signed, but SNS is doing two things:
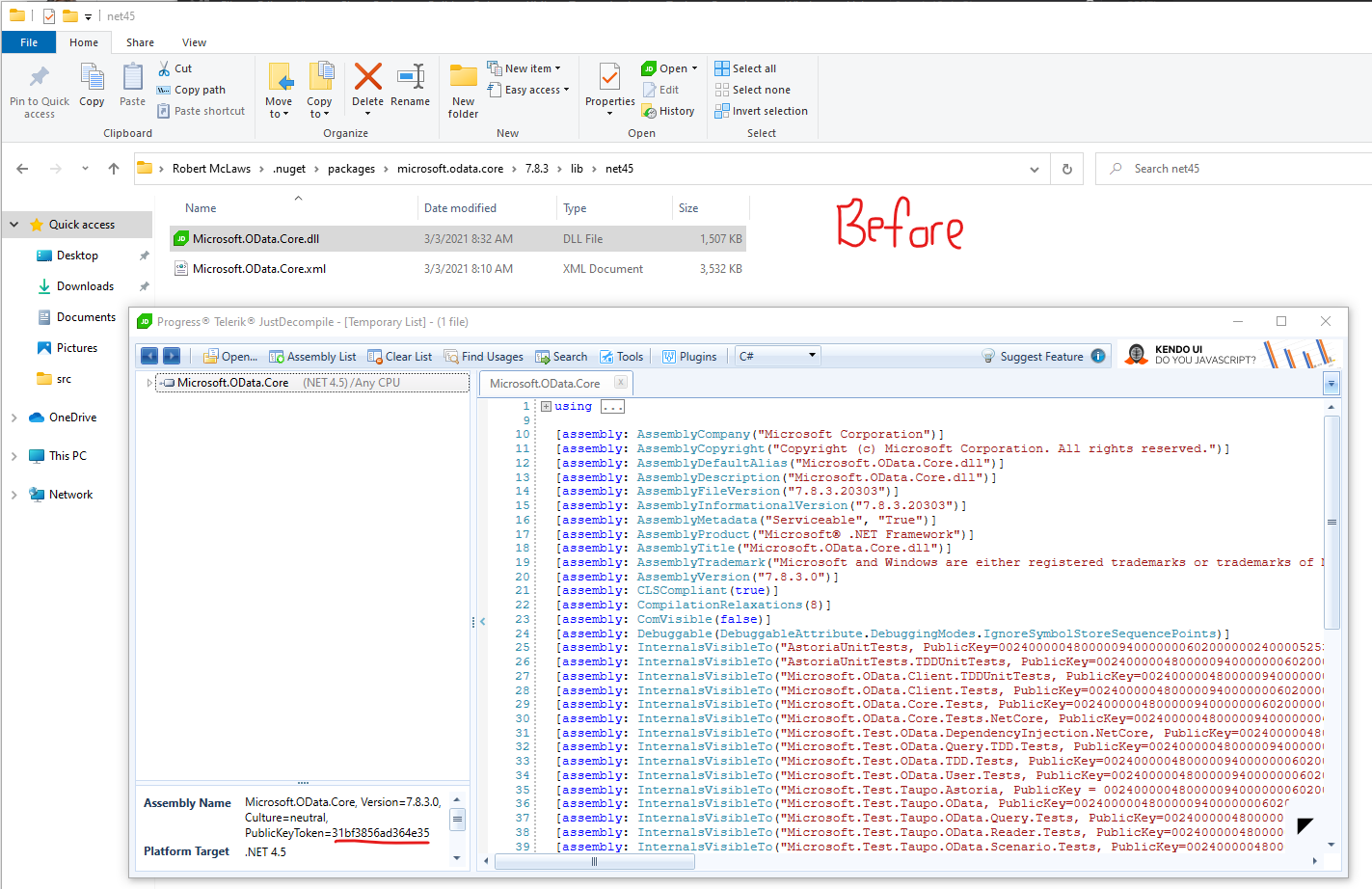
This is the Microsoft.OData.Core binary in the NuGet package cache BEFORE compiling my project with SNS:
This is that binary afterward:
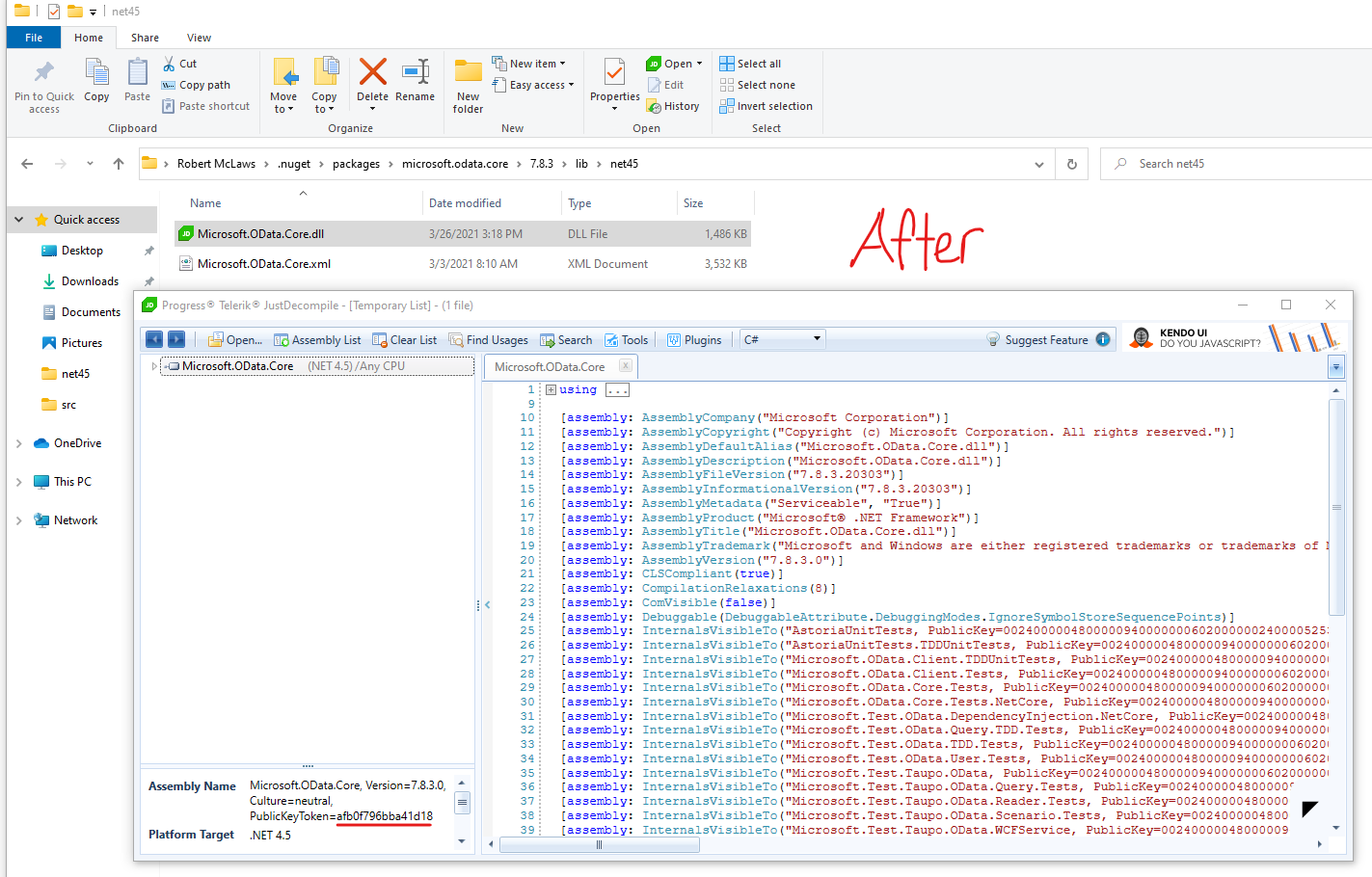
This is breaking all my builds, because once the dependent binaries are modified, the assembly identity is broken, and the build can't find the proper types. And when I say all my builds, I also mean any other application on my machine that also uses those packages.
I've tried several different ways to disable to Targets from executing, with no luck.
Is there any way to quickly get this problem fixed so we can get a new build out? Thanks a bunch!
@brutaldev commented on GitHub (Mar 29, 2021):
Re-signing would be a necessary process since any changes to the assemblies. When this was developed it would simply scan and fix you local "packages" directory so would not impact any other projects since everyone has their own copies.
Due to how packages are shared in a central location these days there would need to be some work done as to how this is managed, resigning the whole packages directory was never a good idea and now it's compounded by everything sharing from the same place and multiple versions etc.
For now you will have to use the build targets to manually point it to your assembly locations rather than it scanning your references: https://github.com/brutaldev/StrongNameSigner#build-process
@robertmclaws commented on GitHub (Mar 29, 2021):
Thanks for the details! Some feedback:
Your package "worked" in the days of /packages folders and separate NuGet manifests. It does not work in the world of SDK projects, tags, and shared package caches. Instead of using brutal tactics, it needs to get surgical about what it is signing, and where it is doing the work.
Happy to potentially assist, if necessary.
@brutaldev commented on GitHub (Mar 31, 2021):
Remove the nuget package and install the console version to use the custom build targets.
I'm not in a position to update this project so you are welcome to fork it and make the changes necessary for modern projects that use the cache. I only use this myself for older projects where signing was important. These days nothing is strong-name signed anymore as it's seen as an anti-pattern and breaks things more than it fixes.
Files are copied to temp locations and backed up, problem is they need to return to the source since a reference is disk location based.
@rcdailey commented on GitHub (Aug 13, 2021):
This just isn't true. For example the yFiles library license requires all libraries using their interfaces to be strong named. Does that suck? Sure does. Is it avoidable? Nope. Open source projects have a lot more freedom on this than established enterprise software projects.
The direction I took was to just copy & paste the console EXE into my repository and set up my own custom targets to invoke it so it processes assemblies in my bin directory. It sucks but it works so far.
@brutaldev commented on GitHub (Dec 30, 2021):
Package cache directories are now correctly ignored in v3.0.6-beta: https://www.nuget.org/packages/Brutal.Dev.StrongNameSigner/3.0.6-beta
@brutaldev commented on GitHub (Dec 30, 2021):
Official release: https://www.nuget.org/packages/Brutal.Dev.StrongNameSigner/3.1.0