mirror of
https://github.com/quasar/Quasar.git
synced 2026-04-26 15:55:58 +03:00
[GH-ISSUE #859] Quasar is being deleted by Antivirus #585
Labels
No labels
bug
bug
cant-reproduce
discussion
duplicate
easy
enhancement
help wanted
improvement
invalid
need more info
pull-request
question
wont-add
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference
starred/Quasar#585
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @ghost on GitHub (Aug 7, 2020).
Original GitHub issue: https://github.com/quasar/Quasar/issues/859
Hi, my issue is that as soon as I download and extract the zip from release version, my antivirus automatically detects the "exe" as virus and deletes it. I can add it as quarantine but that's not a permanent solution for my use case unfortunately, as I can have to run this program on many client machines and can't ask them to first quarantine the exe path.
What is the solution for it? What are your thoughts please?
Now, as per my research, I believe that signing the exe with a valid certificate such as "DigiCert" (used by Mozilla) will resolve the issue. I used a site "https://www.virustotal.com/" to scan the "Quasar.exe" file and found 44 issues. I self-signed it then and it produced only 24 errors, but still it's not perfect (screenshots attached for Quasar.exe scan)
My question is, do I absolutely need to purchase a certificate from valid CA like Digicert and sign the exe to resolve this problem? Would just signing be enough or it can also flag the app. while it's executing? And if certificate is not required, what are the ways I can remove this check? Maybe I have to change source code (Assembly file) or something else?
Please let me know. This is an urgent project and I'm on a very strict deadline so I would very much appreciate your help here!
Kindest Regards,
Solat
@MaxXor commented on GitHub (Aug 7, 2020):
Hey, your options are to remotely add the AV exception first and then deploy the Quasar client or to try removing the unnecessary functions for your use-case from the Quasar client in the source code to see if it's still detected once compiled. Unfortunately Quasar is sometimes used in questionable circumstances which makes it impossible to remove the AV detections.
@ghost commented on GitHub (Aug 7, 2020):
Thanks for replying. Now, I think I need all the functionality of the client and can't remove things per-say. But, what about the code signing thing? Would that work out? Like if I purchase a certificate from "DigiCert" let's say (Mozilla uses it) and then use it to sign the exe, would that suffice?
Or can the exe still be flagged while it's running?
@MaxXor commented on GitHub (Aug 7, 2020):
I think it might depend on the AV in use. Check out if all signed software is trusted by default.
@ghost commented on GitHub (Aug 7, 2020):
Yes, they are. But what I was saying, is while the client is running, are there chances that app. could still be flagged? Also, has any other user ever actually mentioned this issue I'm facing?
@ghost commented on GitHub (Aug 8, 2020):
Please respond on the last question!
@MaxXor commented on GitHub (Aug 8, 2020):
There is no way I can tell you whether signing the client binary will 100% work for your use case. Please do your own research. Yes, other users have faced the same issue, see here: https://github.com/quasar/Quasar/issues?q=is%3Aissue+antivirus+is%3Aclosed
Don't forget when deploying Quasar, the client binaries also need to be signed.
@ghost commented on GitHub (Aug 8, 2020):
Thank you for the reply. Just 1 quick question. I checked the following closed question:
https://github.com/quasar/Quasar/issues/658
And you mentioned "There are some suspicious functions included, that's why it's detect by antivirus." Can you please point them out? So, maybe I can decide to remove them from the code?
Also, what are your thoughts on the following solution suggested by another user?
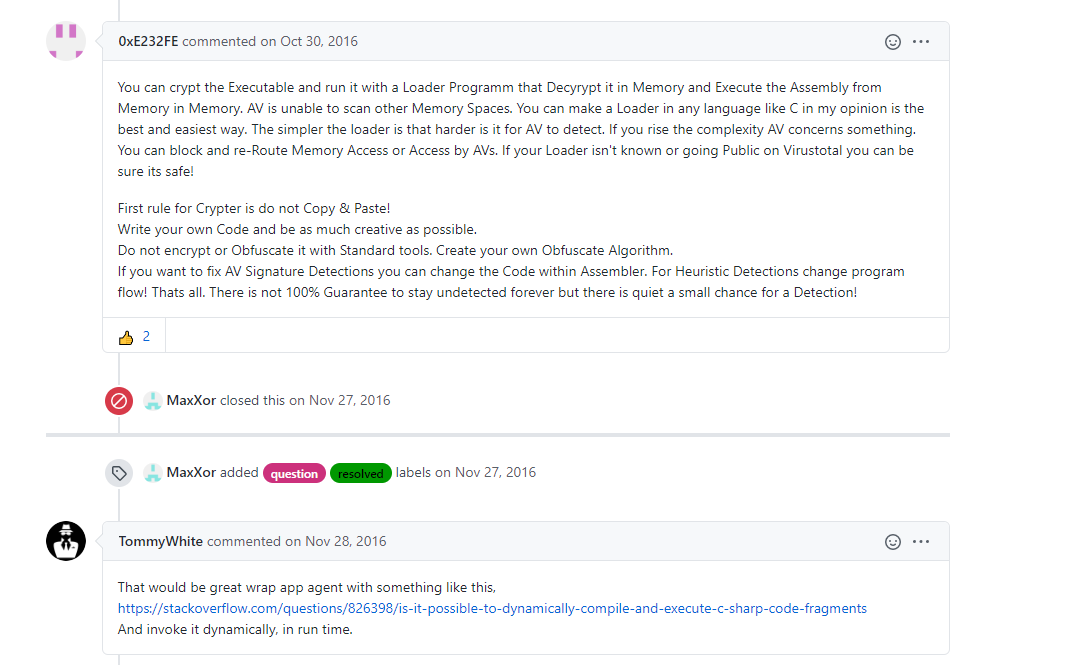
Thank you in advance
@MaxXor commented on GitHub (Aug 8, 2020):
That was 2 years ago. Most of the functions are removed by now. I suspect the password recovery functions to play an important role for the detection. You can try to remove these.
@ghost commented on GitHub (Aug 8, 2020):
Sure, I'll take a look. And any idea about that "App Loader" suggestion? Would that work out in this use case?
@MaxXor commented on GitHub (Aug 8, 2020):
It's lots of trying to get it right. Definitely not easy.
@ghost commented on GitHub (Aug 8, 2020):
Thank you for the answers Max!
Now, I contacted my client and he told me to just keep "Screen mirroring and task manager" for the client app. I believe, we can get through the AV detection then, right?
@MaxXor commented on GitHub (Aug 8, 2020):
Try it out.
@ghost commented on GitHub (Aug 8, 2020):
Sure, thank you so much.
@BurntDog commented on GitHub (Dec 29, 2020):
Not to smart for using Virustotal to check tools like this, noob 101....