mirror of
https://github.com/cbeuw/Cloak.git
synced 2026-04-27 05:25:52 +03:00
[GH-ISSUE #185] Update chrome fingerprint to latest version #153
Labels
No labels
pull-request
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference
starred/Cloak#153
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @HirbodBehnam on GitHub (Mar 23, 2022).
Original GitHub issue: https://github.com/cbeuw/Cloak/issues/185
Hello
I think today some internet providers in Iran blocked chrome fingerprint version 97 and older. This means that cloak also could not connect using chrome fingerprint (Firefox is fine)
I did a check. Apparently this is the current fingerprint of chrome. Is it possible for you to update it?
Thanks
Update: I checked and it looks like that cloak uses this fingerprint for chrome. One big difference is that cloak informs the server that it supports TLS 1.1 and 1.0 while chrome doesn't.
@HirbodBehnam commented on GitHub (Mar 23, 2022):
I also suspect that cloak with Firefox fingerprint sometimes connect and sometimes it doesn't. I'm not really sure why...
@HirbodBehnam commented on GitHub (Mar 23, 2022):
Ok I've seen some strange behavior. I might not be a fingerprint problem. On windows, even chrome fingerprint randomly connects. I used wireshark and apparently, even the server hello comes in! But then, only client can send data to server. This is obviously has to do something with Iran filtering system. I'm not quite sure if something triggers it from client hello or sever hello. I'll try to investigate...
@HirbodBehnam commented on GitHub (Mar 23, 2022):
So I found a temporary solution.
github.com/cbeuw/Cloak@68f47f1d49/internal/client/chrome.go (L65-L74)At first change line 65 string to
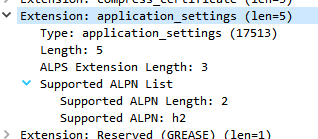
069A9A03040303. This will disable the TLS 1.0 and 1.1. Then change line 74's make size to233-len(ext[1]). This simply adds 4 bytes to padding because we removed 4 bytes from client hello.In this way, the fingerprint of client hello changes to this (still not chrome but me and my friend checked and it works in Iran)
If you want, I can open a pull request to implement this change here but I prefer make it identical to chrome. How to do this? Apparently, chrome also sends some unknown field in client hello. utls says that you have to add this extension to TLS:
Which I don't know what it is but I'll search...
Update: This is something called application settings in wireshark: